Description
Tutorial to setup a nextcloud server (equivalent to google drive but free and adapted to collective organisations) on a single board computer (photovoltaics powered)
This tutorial is not really "lowtech" at first look because we talk about computers and photovoltaics
However it is as didactic as possible and follows a lowtech philosophy to share knowledge, avoid unreachable tech by information rentention, complexification by design, or proprietary
dependance by design.
We also give sizign tools for photovoltaics with a few explanation.
It's up to to you to size your computer working hours on a sun schedule, ie respecting human temporalities.
Nextcloud (framasoft offers a service here: https://www.frama.space/abc/fr ) is a cool service to organise collectively and allows to share files, have a directory, a chat, work cooperatively on libreoffice files, and even do visios. We can also imagine mobile infokisosks on this principle.
The tutorial puts into question the vpn market, the phtovoltaics with brand new and expensive batteries (in reality photovoltaics has become too competitive compared to petrleum and even more compared to nuclear power!), and the gafam market and their surveillance design is damaging trust and social links.
The commands are those for a debian system
Finally, the tutorial is made iwth 4G modem (and a wired connection to orange pi which has no wifi card by default), and is updated on this 10th of april for a raspberry pi connected
to a "shared wifi" of your telephone (see stage 6 for a wifi in wpa3 and stage 16 for a wifi in wpa2)
Sommaire
Sommaire
- 1 Description
- 2 Sommaire
- 3 Introduction
- 4 Étape 1 - Tools
- 5 Étape 2 - Nextcloud installation 1/4
- 6 Étape 3 - Installation de nextcloud 2/4
- 7 Étape 4 - Installation de nextcloud 3/4
- 8 Étape 5 - Installation de nextcloud 4/4
- 9 Étape 6 - configuration du reseau local ethernet ou wifi
- 10 Étape 7 - configuration d'un vpn wireguard pour rendre accessible votre serveur depuis une box 4g ou un modem 4g
- 11 Étape 8 - configuration d'un vpn openvpn pour rendre accessible votre serveur depuis une box 4g ou un modem 4g
- 12 Étape 9 - Rediriger les requetes du serveur vpn vers le orange pi-raspberry pi
- 13 Étape 10 - Nom de domaine et adresse fixe
- 14 Étape 11 - Configuration https sur serveur gandi vpn
- 15 Étape 12 - Configuration https sur dietpi si vous etes branché en box
- 16 Étape 13 - Rendre votre serveur nomade et autonome énergétiquement en photovoltaique
- 17 Étape 14 - Montage et test
- 18 Étape 15 - Securisation du serveur
- 19 Étape 16 - Activer le wifi lors de l'installation (par exemple avec un raspberry)
- 20 Notes et références
- 21 Commentaires
Introduction
Tutorial to setup a nextcloud server (equivalent to google drive but free and adapted to collective organisations) on a single board computer (photovoltaics powered)
This tutorial is not really "lowtech" at first look because we talk about computers and photovoltaics
However it is as didactic as possible and follows a lowtech philosophy to share knowledge, avoid unreachable tech by information rentention, complexification by design, or proprietary dependance by design.
We also give sizign tools for photovoltaics with a few explanation. It's up to to you to size your computer working hours on a sun schedule, ie respecting human temporalities.
Nextcloud (framasoft offers a service here: https://www.frama.space/abc/fr ) is a cool service to organise collectively and allows to share files, have a directory, a chat, work cooperatively on libreoffice files, and even do visios.
We can also imagine mobile infokisosks on this principle.
The tutorial puts into question the vpn market, the phtovoltaics with brand new and expensive batteries (in reality photovoltaics has become too competitive compared to petrleum and even more compared to nuclear power!), and the gafam market and their surveillance design which is damaging trust and social links.
The commands are those for a debian system
Finally, the tutorial is made iwth 4G modem (and a wired connection to orange pi which has no wifi card by default), and is updated on this 10th of april for a raspberry pi connected to a "shared wifi" of your telephone (see stage 6 for a wifi in wpa3 and stage 16 for a wifi in wpa2)
See https://solar.lowtechmagazine.com/ to go further with the low tech internet insights (in particular "how to create a lowtech internet"?)
Matériaux
Outils
autonomie.ods
Étape 1 - Tools
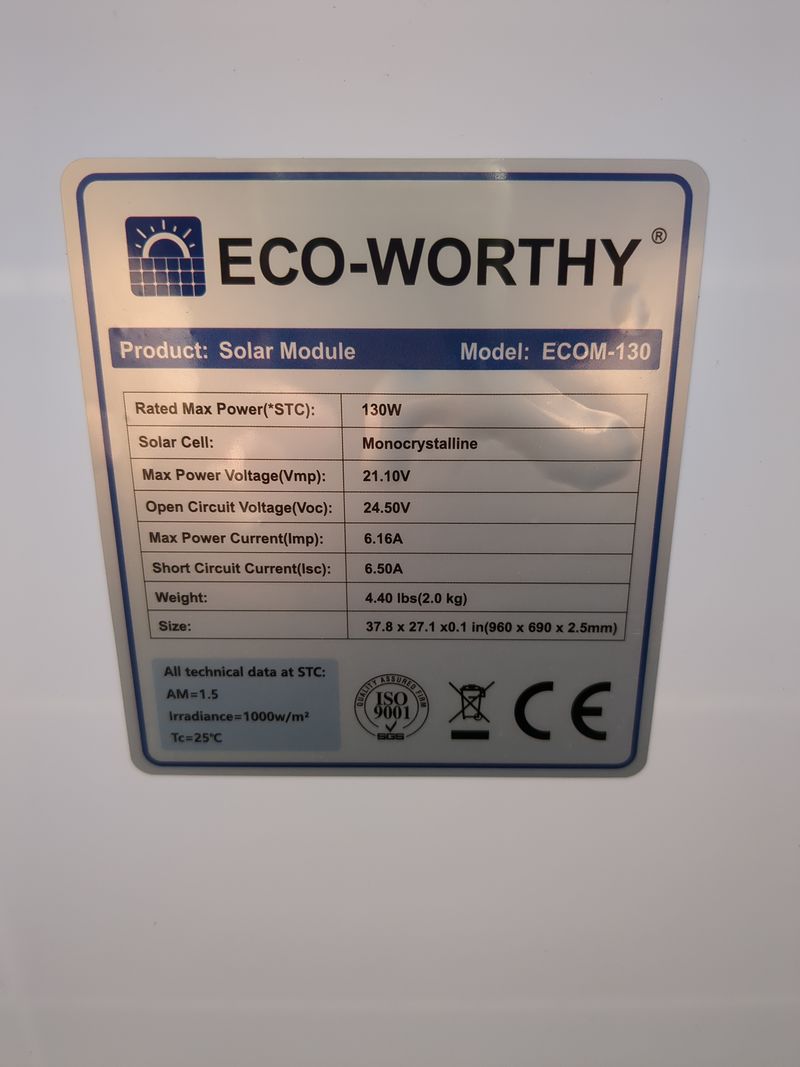
The links to the photovoltaics material are in the autonomie.ods file (readable with libreoffice) attached to this tutorial.
- raspberry pi :
42€ on leboncoin
-Orange pi :
single board computer: Orange pi 5
single board computer with 4,8,16 or 32 Go of ram
2,4Ghz ARM Cortex-A55 CPU
This card is compatible with nvme pcie 2.0 hard drives (2242 or 2230, pcie is retrocompatible ie 3.0, 4.0 and 5.0 work with lower speed on orange pi 5)
Same principle as here but a bit more powerful and we can plug a hard drive (useful for nextcloud which is made to host files) and it starts automatically on a usb stick
Price: 143€ brand new on aliexpress in version 16 Go on the 2nd of august 2023
Second hand on leboncoin: we find more easily raspberry pi at around 100€.
It is necessary to buy a small box at 10€ (or make one) to avoid a naked single board computer
-hard drive
Here we use a kingston usb stick of 32Go and a nvme samsung 512Go card
We can plug a hard drive of higher capacity in usb, or a nvme card (nvme pcie 2.0 ssd 2242 or 2230) compatible with pcie 3.0 4.0 and above but the speed is reduced
A nvme samsung 2242 card of 500Go is about 50€ on the 2nd of august 2023.
-usb stick : 10€
- rj45 cable: 5€
-Internet box or 4G modem according to your internet connection
-solar pannel: here we use a flexible 120W pannel bougth 115€ brand new but we can find second hand ones at 30€ on leboncoin for an equivalente peak power.
Note: for the theoretical need. See file autonomy.ods
-second hand battery: use the previous lead acid battery of your car when it crashes when it's too hot in summer!
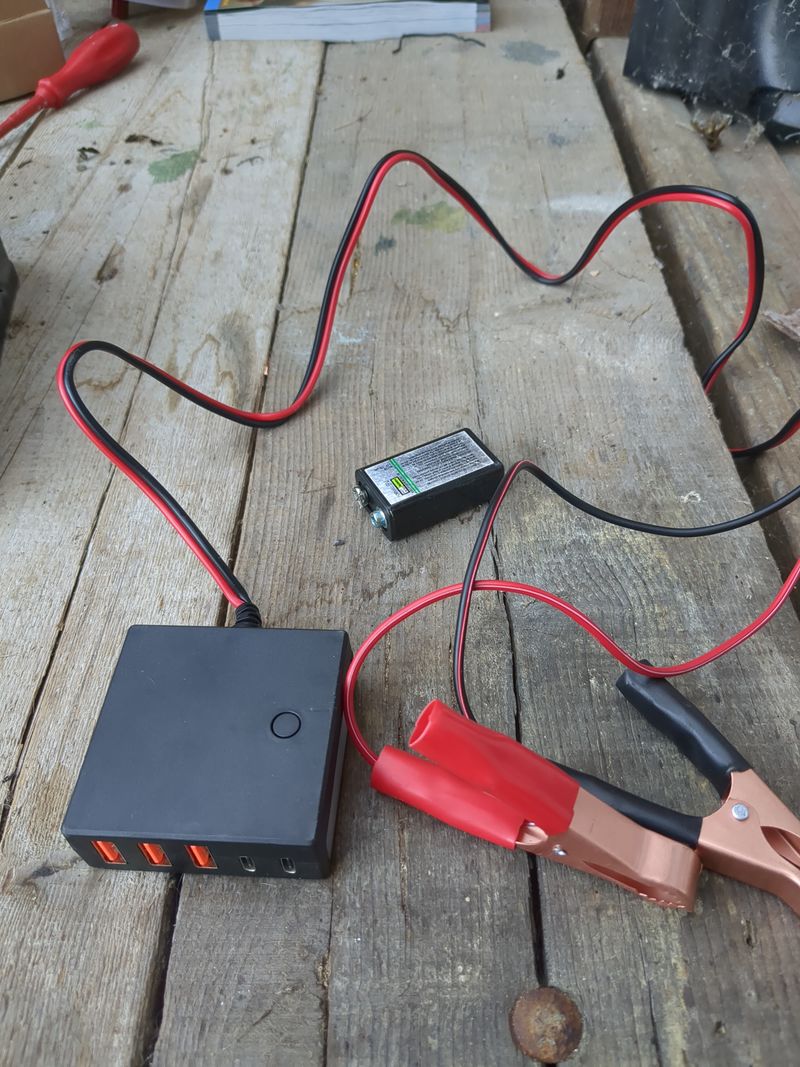
-12V/24V-usb 5V battery converter: 20€ avoid amazon if you can
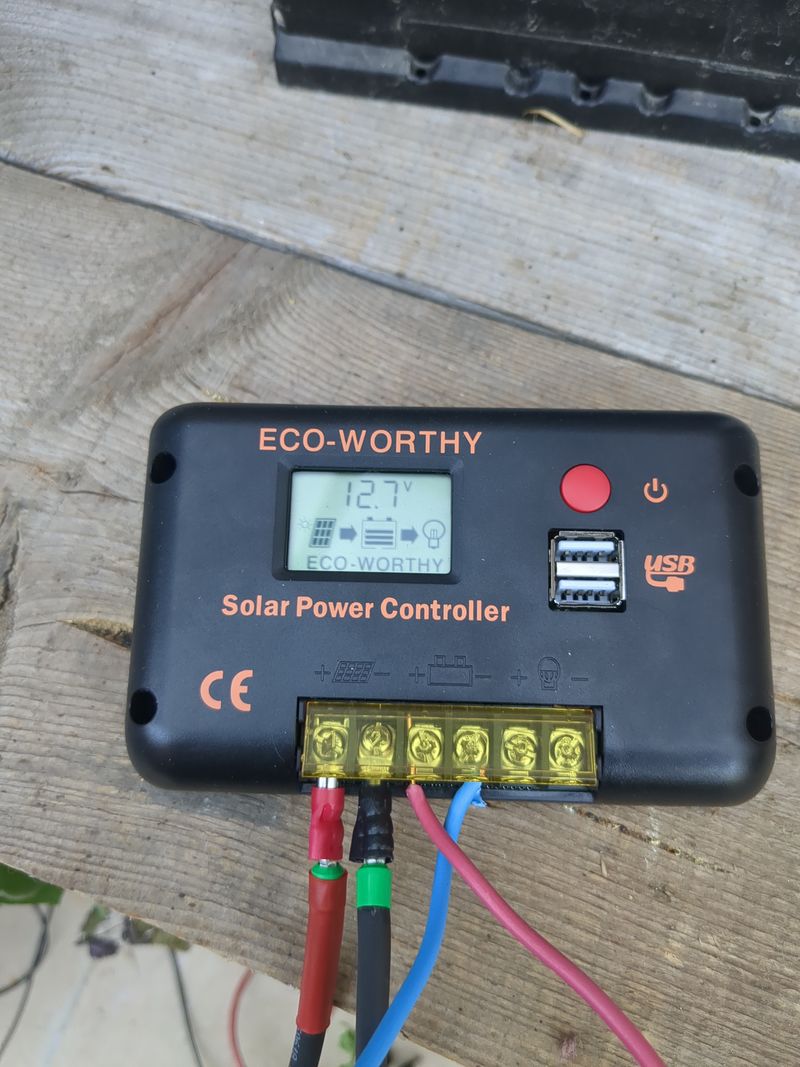
- pwm regulator 30A: 30€ brand new if you dont buy corporate brand
- DRL (day/night switch 13V): 1,5€ brand new
(key word "Kit de feux de jour à LED pour voiture, contrôleur marche/arrêt automatique DRL" in french)
-electric mc4 cable: 20€
Total second hand price for orangepi: 256,50€
Total brand new price for orangepi: 431,50€
Total second hand price for raspberry: 165€
See autonomie.ods
-
Étape 2 - Nextcloud installation 1/4
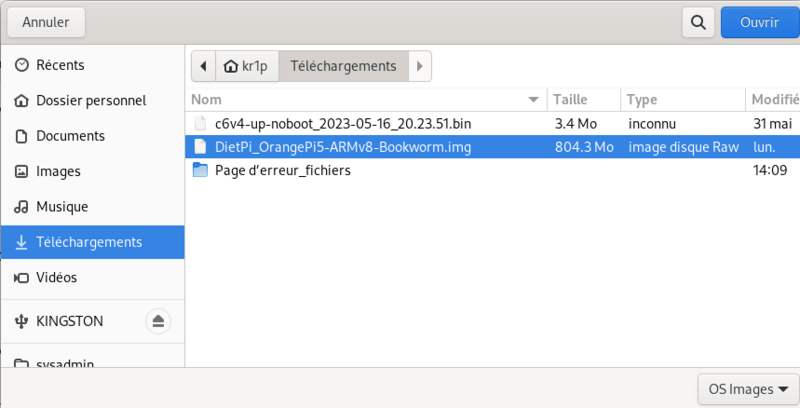
1. Download dietpi and prepare your usb stick
For installation, i recommend using diepti. It is interesting in particular for it is lightweight for single board computers, but also because the automatic installation of free software
with a relatively "user friendly" menu. We can mention among all the installable software at boot (https://dietpi.com/dietpi-software.html)
domotic apps, interesting to save energy based on weather, but also tor relay to contribute to the relatively anonymous tor network, interesting for any "eco-terrorist" we are.
We must also mention "younohost"(https://yunohost.org/fr) which is french and who does the same job as dietpi for raspberry and which is also "user friendly" or even more. I have not yet tested yunohost because i had put aside raspberry pi after too many weird mouse bugs. My research to avoid these weird mouse bugs have not concluded positively to any solution (purism, odroid, raspberry, orangpi, macbook, windows, see security section), i can only send a feedback on what i have really tried.
( for younohost : https://yunohost.org/fr/install/hardware:arm)
Select the single board computer (orange pi in the present case) and then download
Unzip the obtained archive
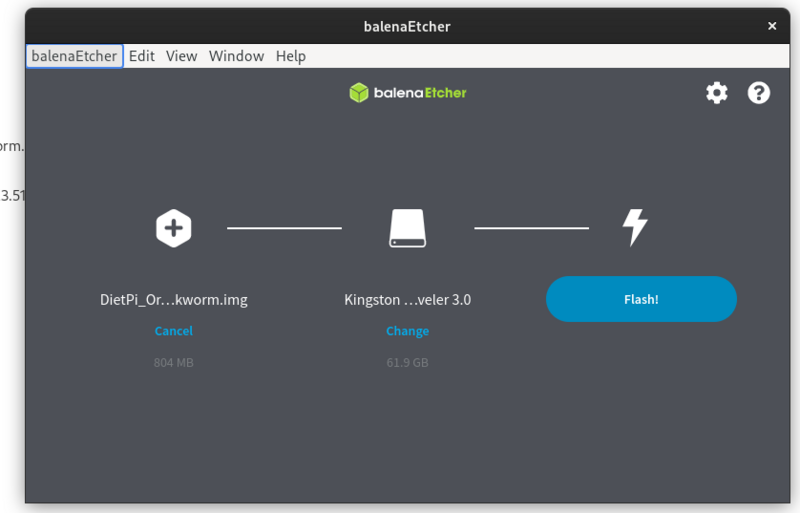
Use balena etcher to create a bootable usb stick to install dietpi on your single board computer (orange pi 5 in the present case but it works the same on other single board computers)
https://etcher.balena.io/#download-etcher
Double click on the downloaded file
Select the dietpi downloaded image, select your usb stick, click on flash.
You only need to plug the usb stick on the orangepi and it will boot automatically on the usb stick.
For a raspberry pi, we use a sd card but we can configure the usb boot as well (see here:https://makerhelp.fr/booter-un-raspberry-pi-4-sur-un-disque-dur-ou-un-ssd-en-usb )
Install nextcloud
Power your orangepi/raspberrypi with the usb stick plugged.
The default login at boot is root and the password is dietpi.
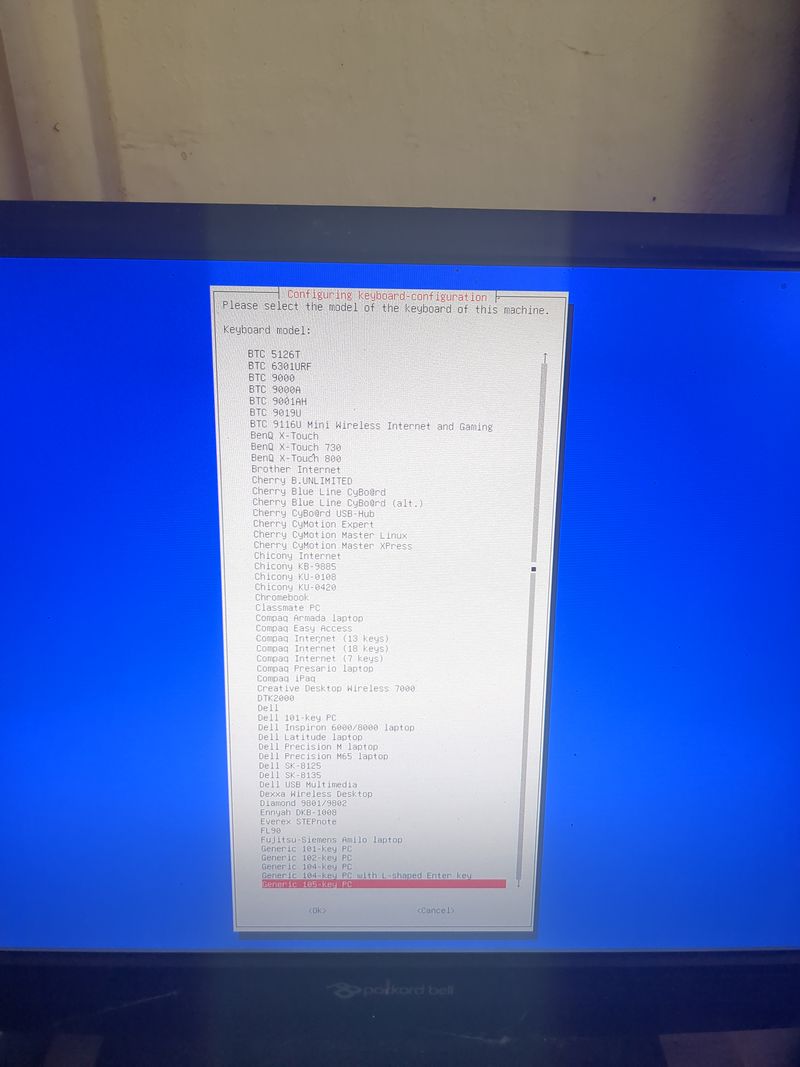
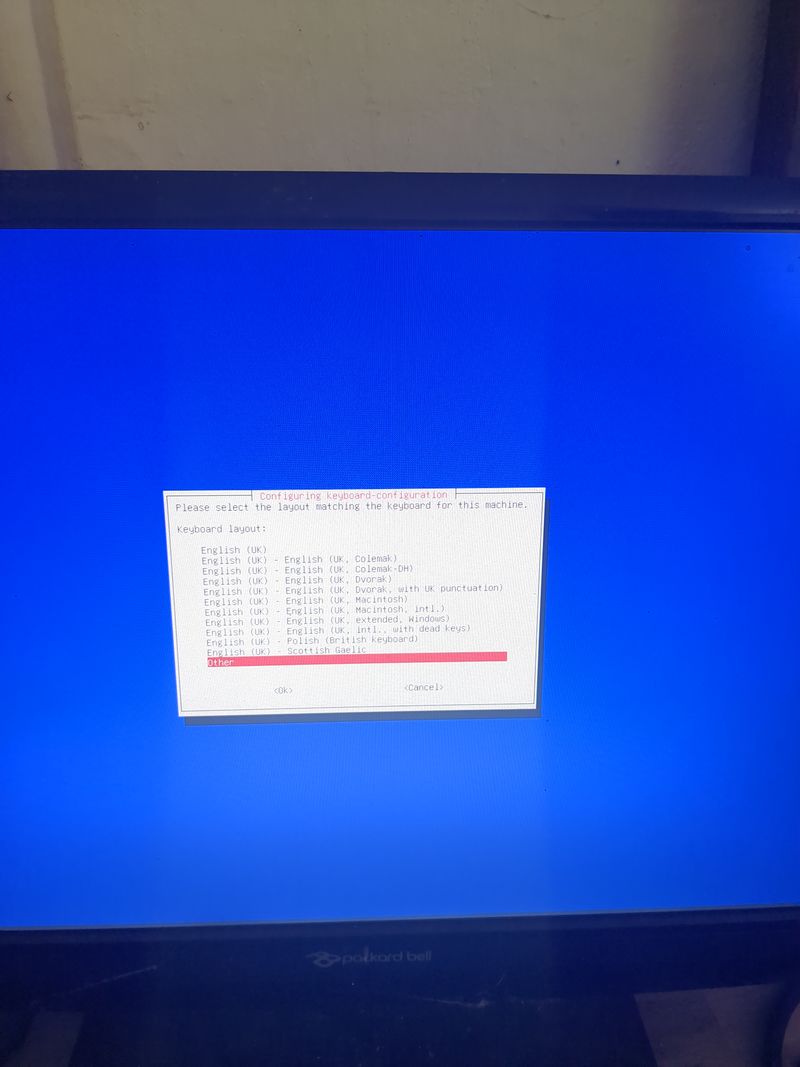
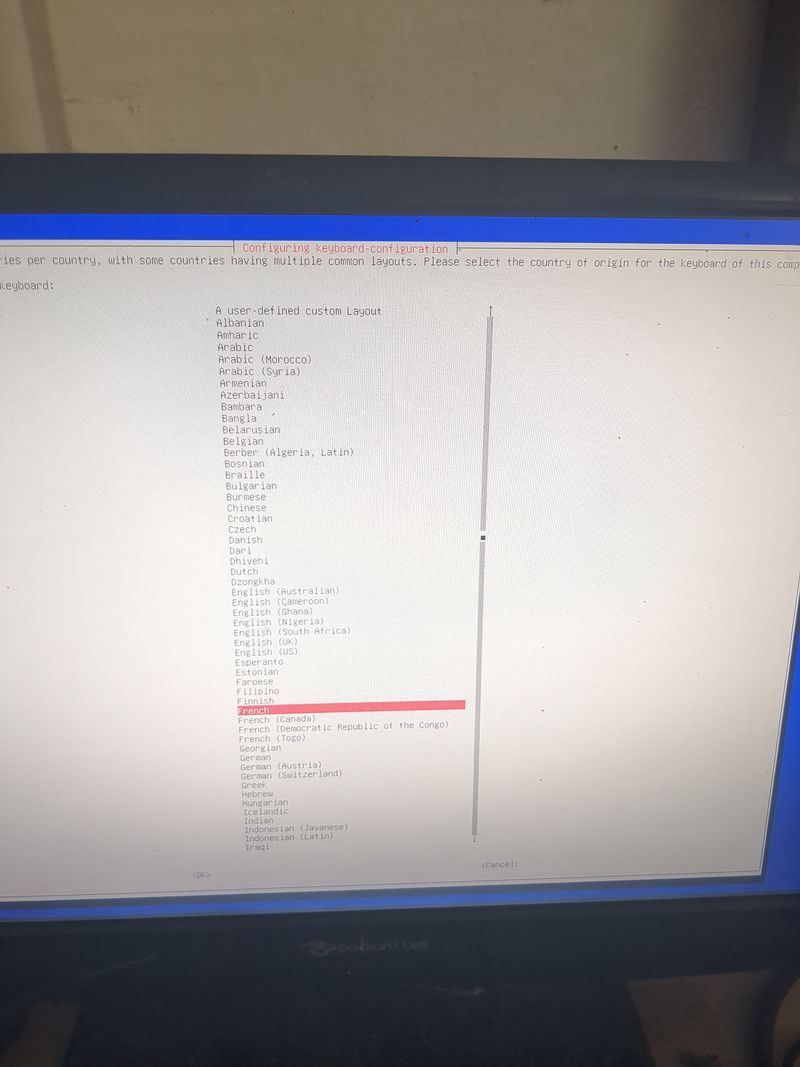
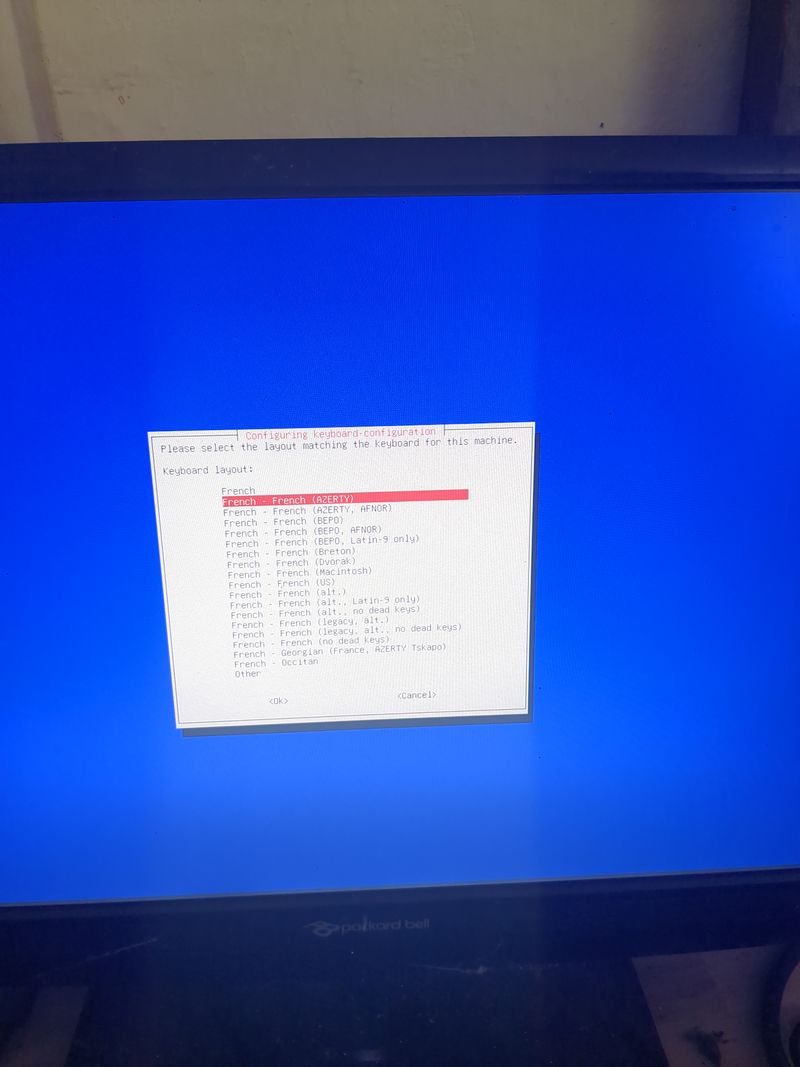
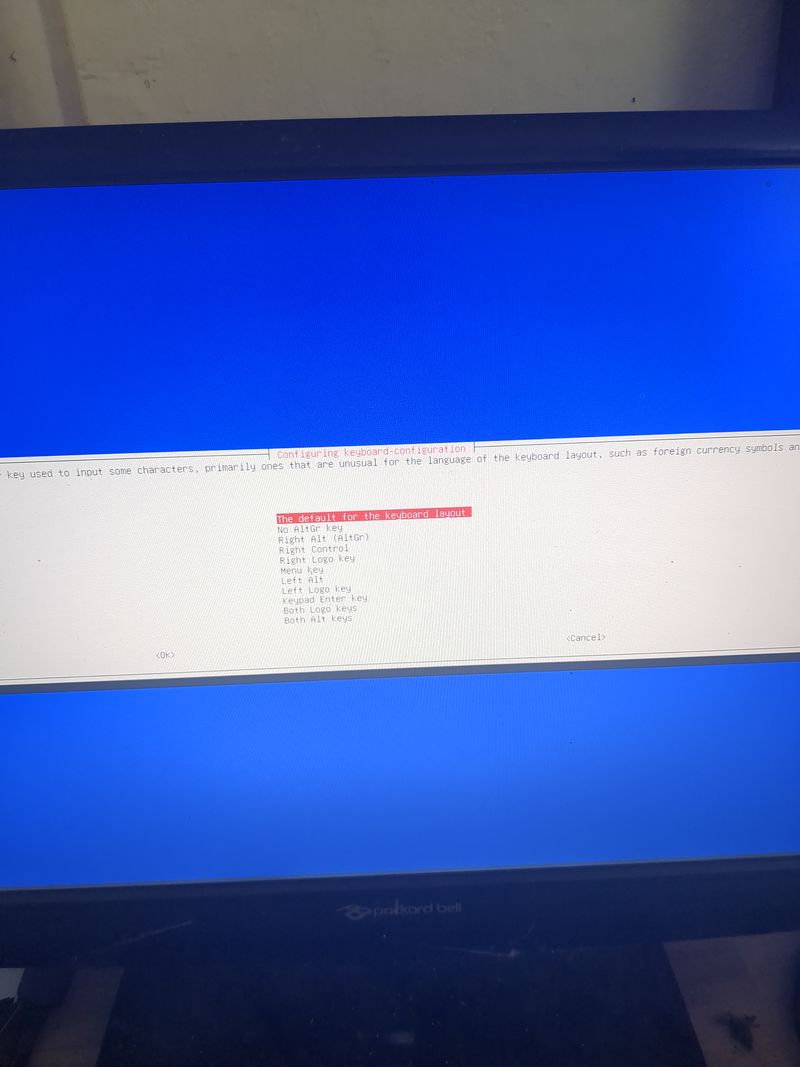
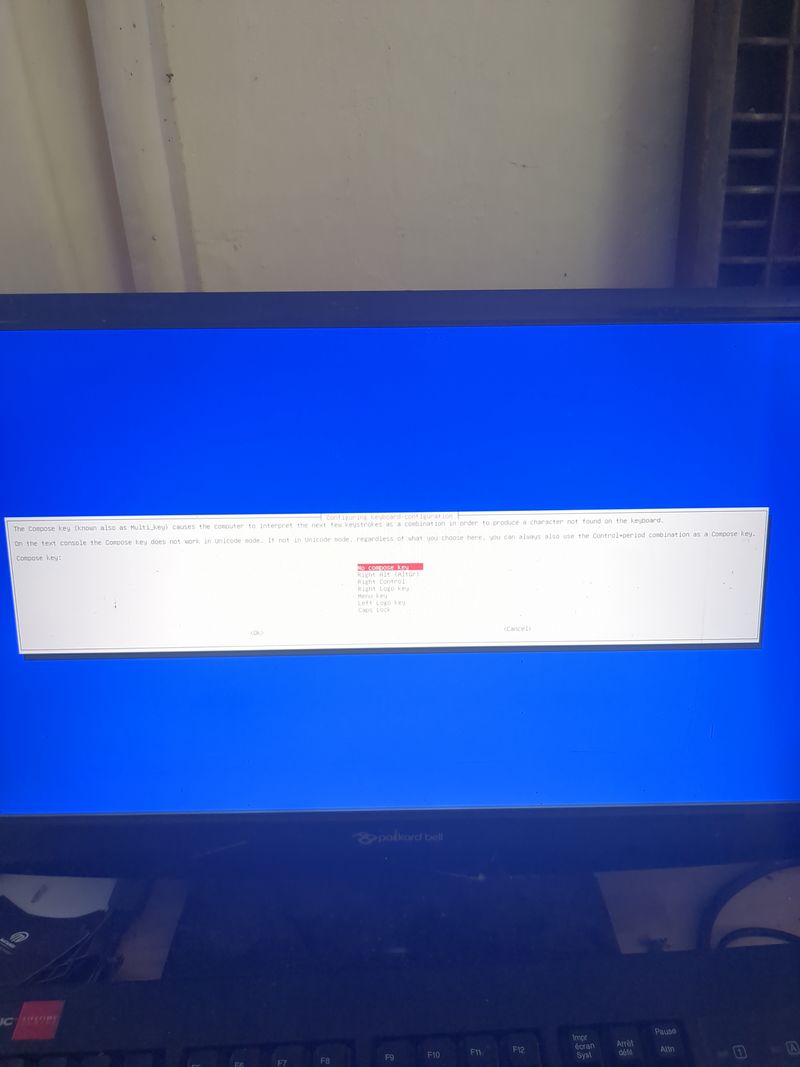
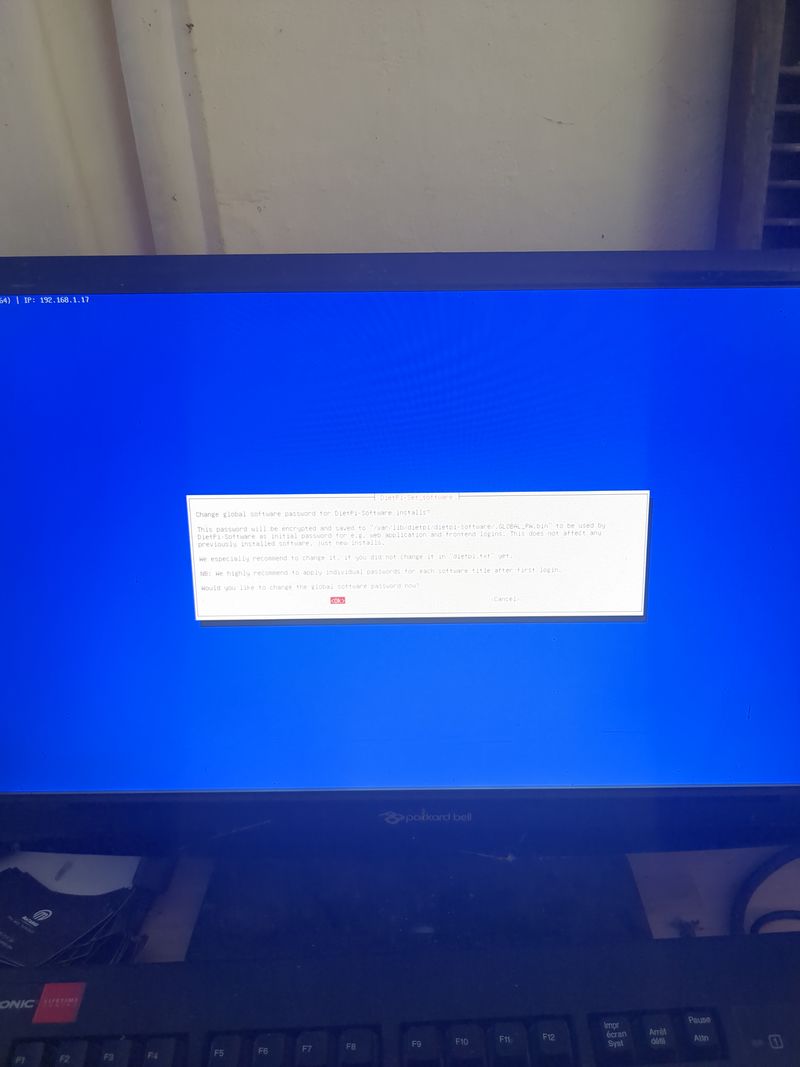
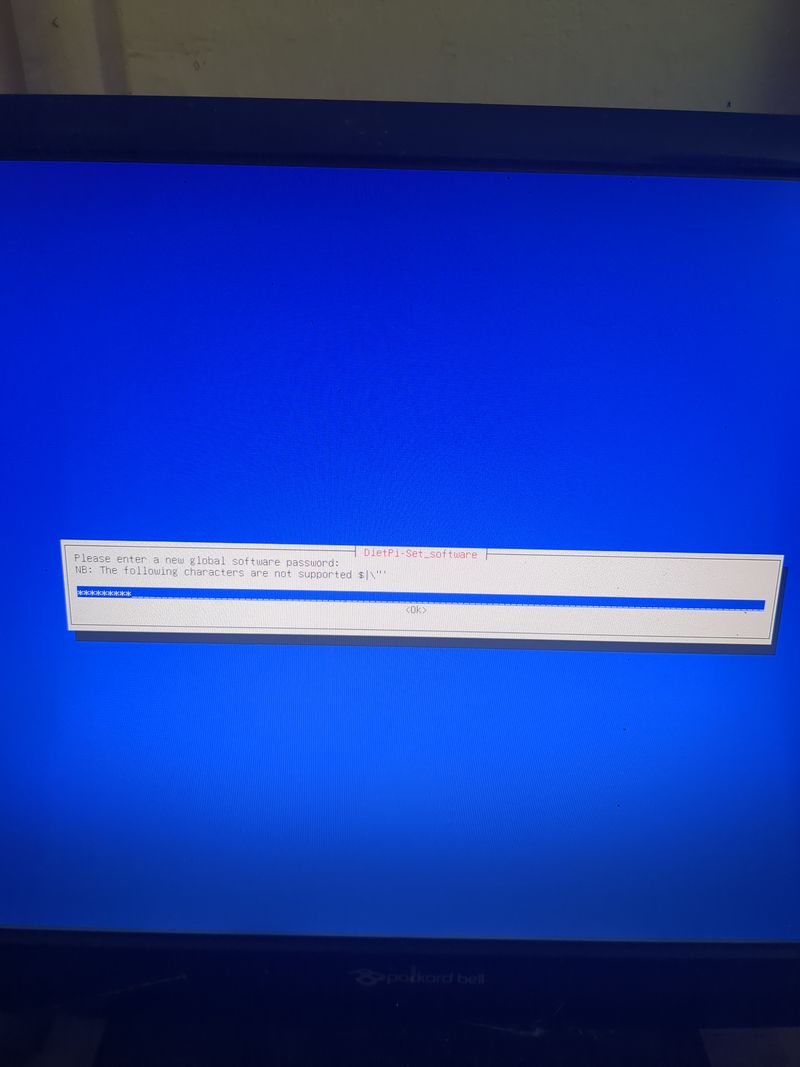
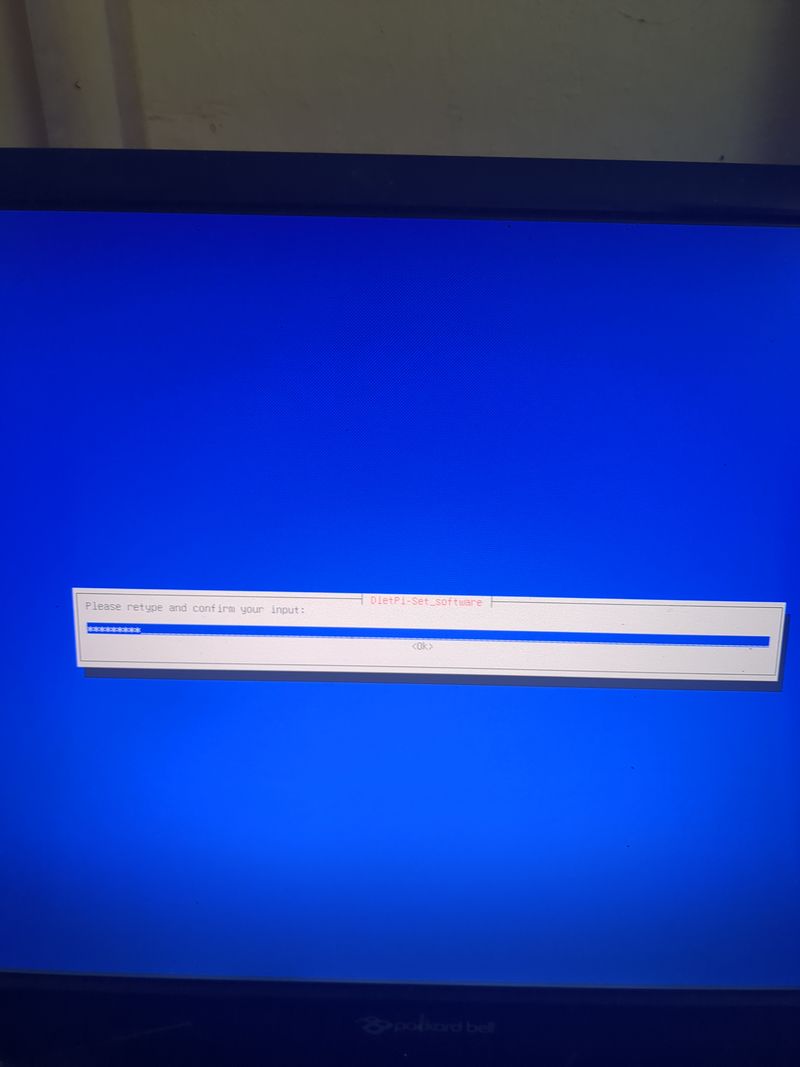
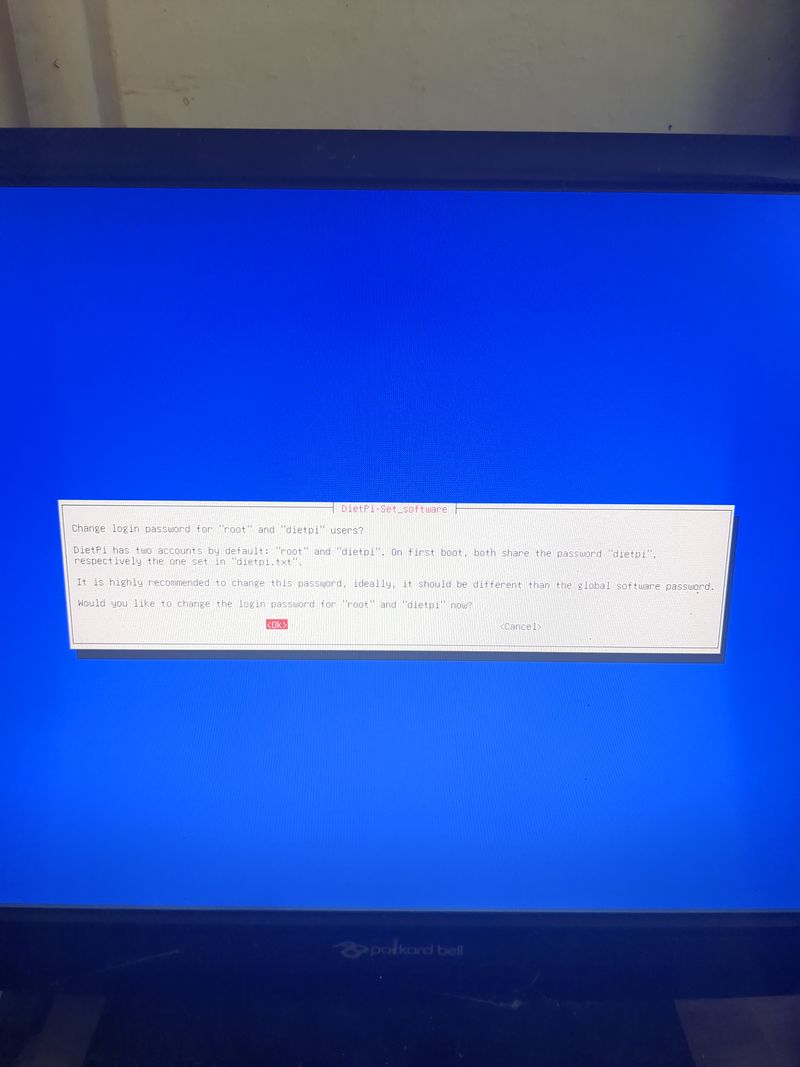
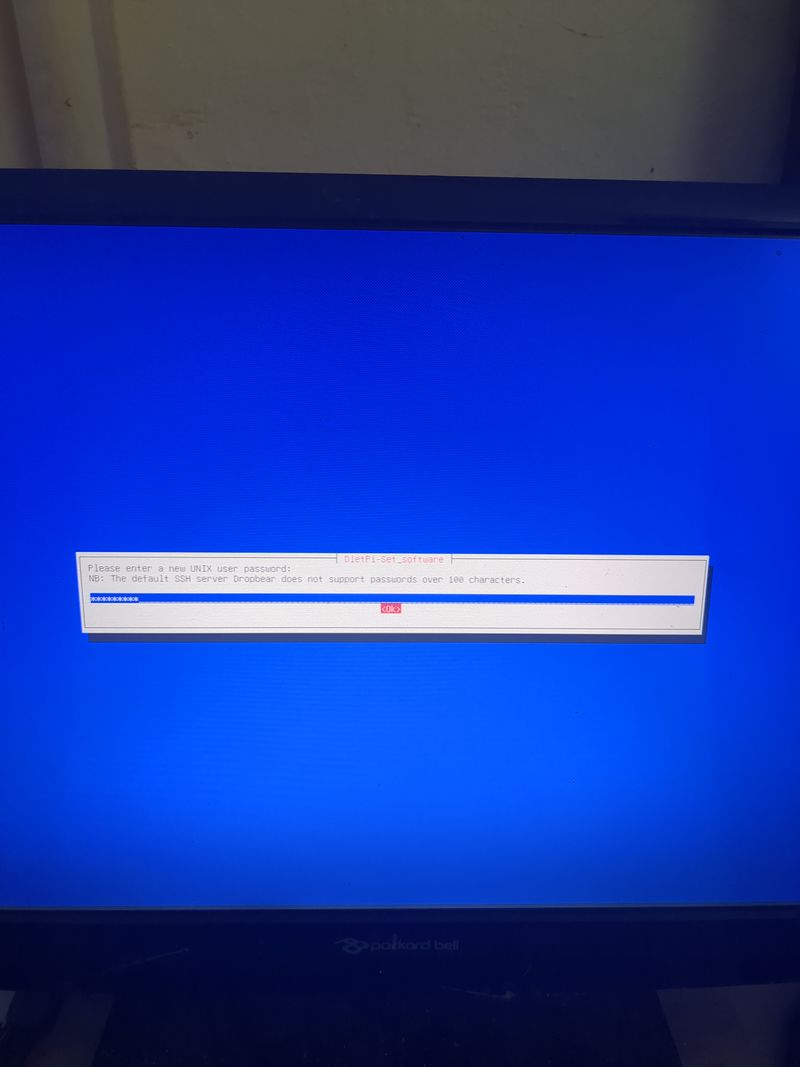
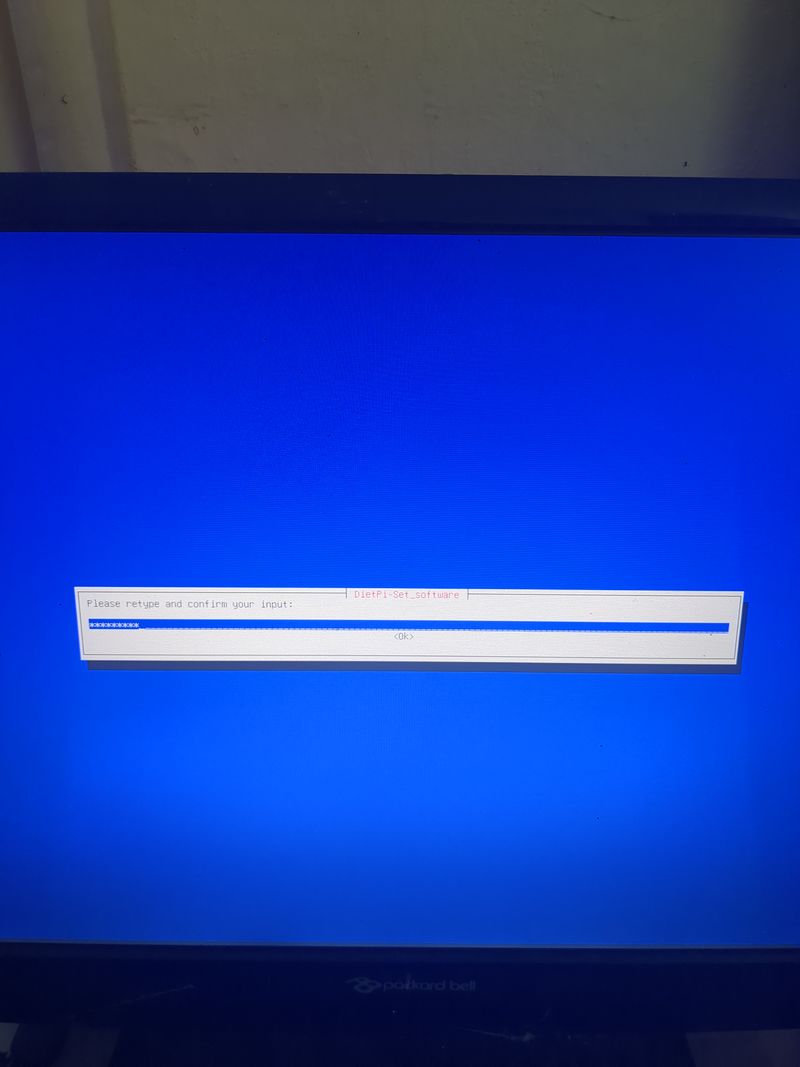
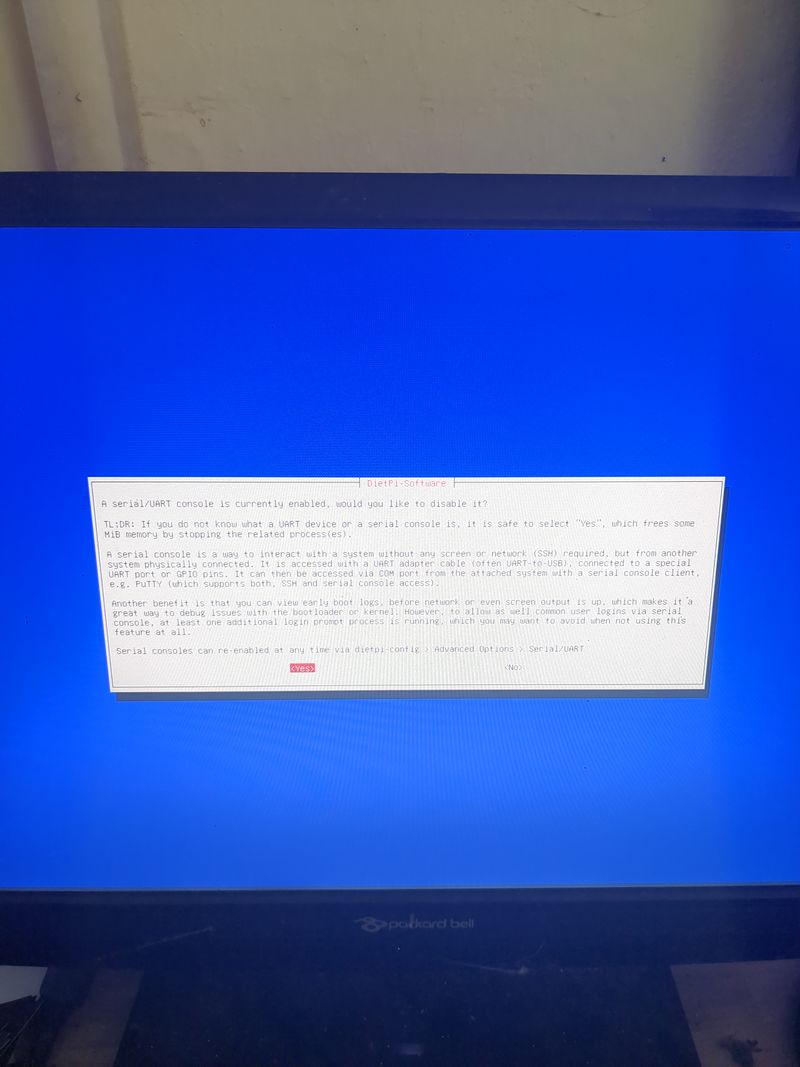
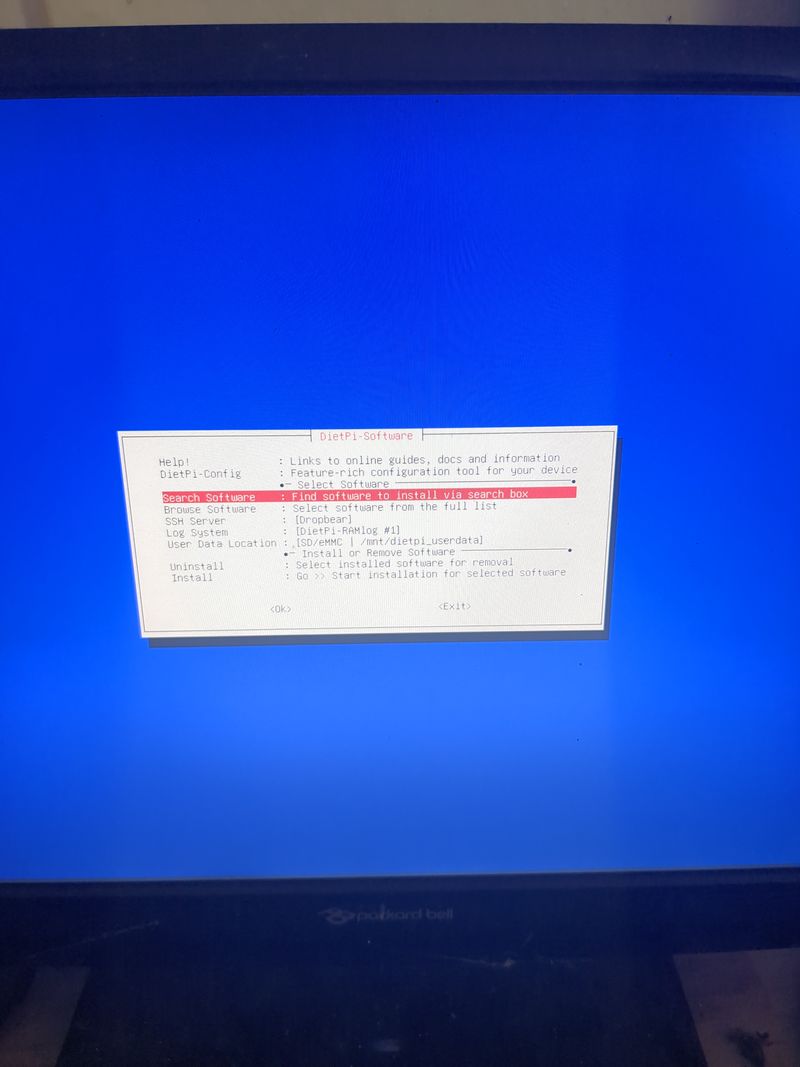
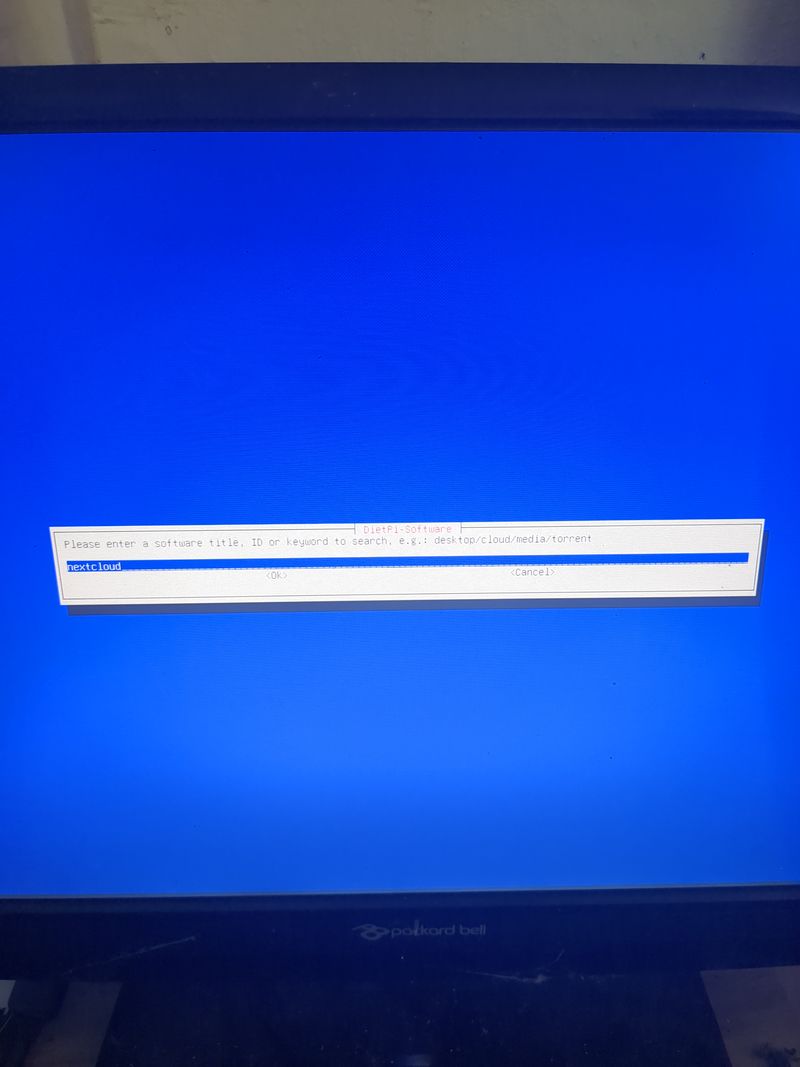
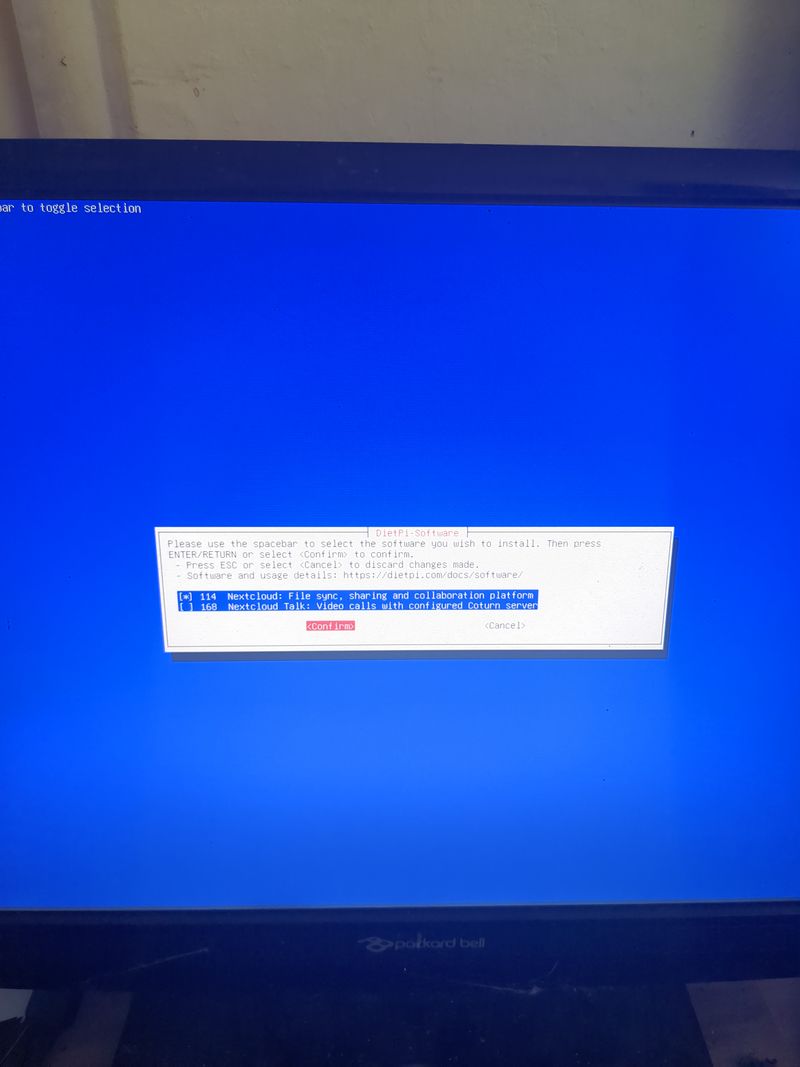
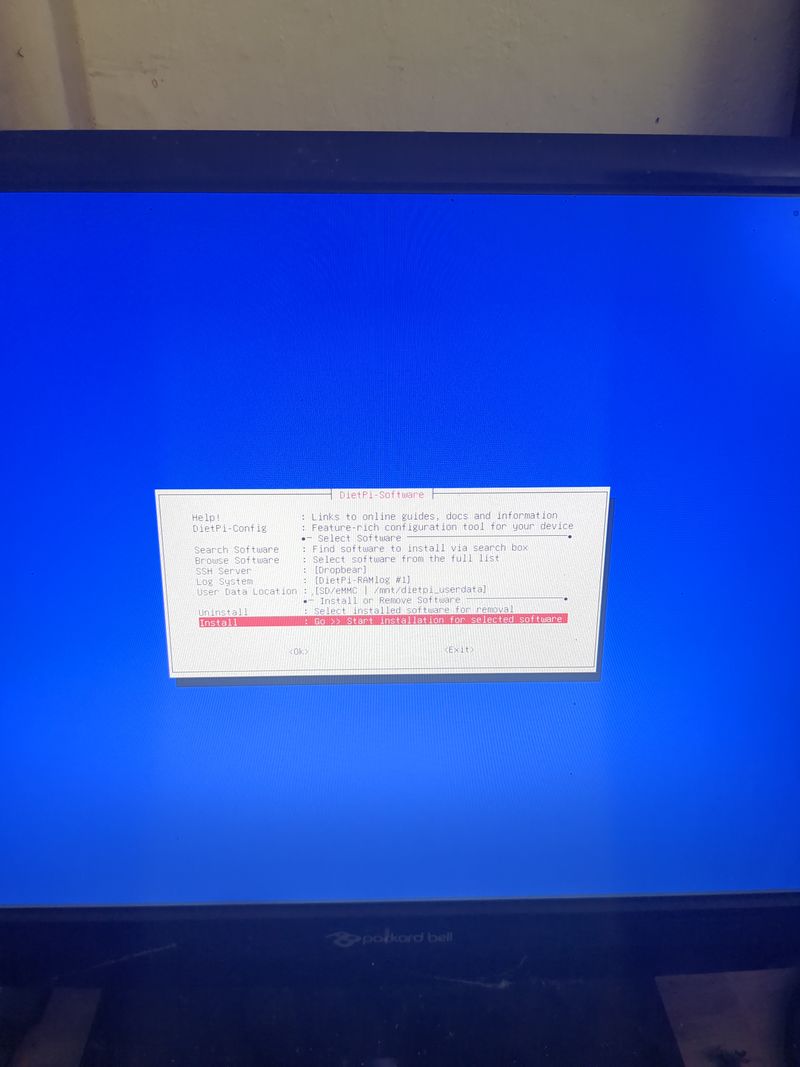
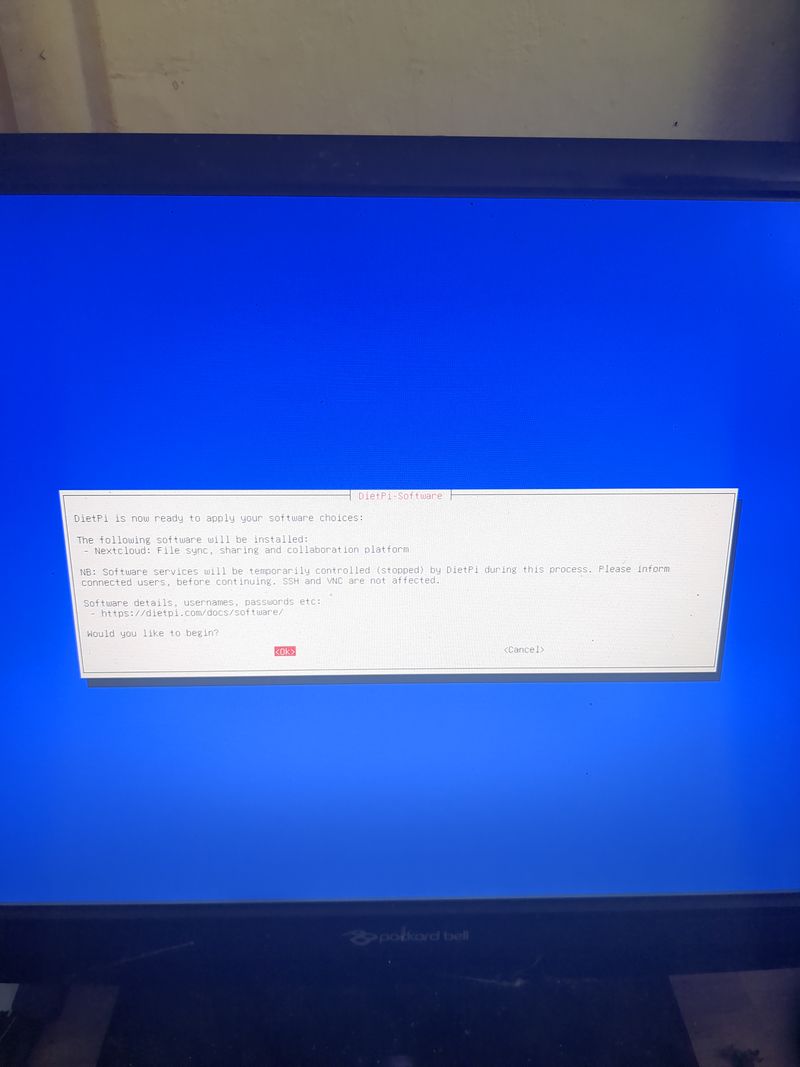
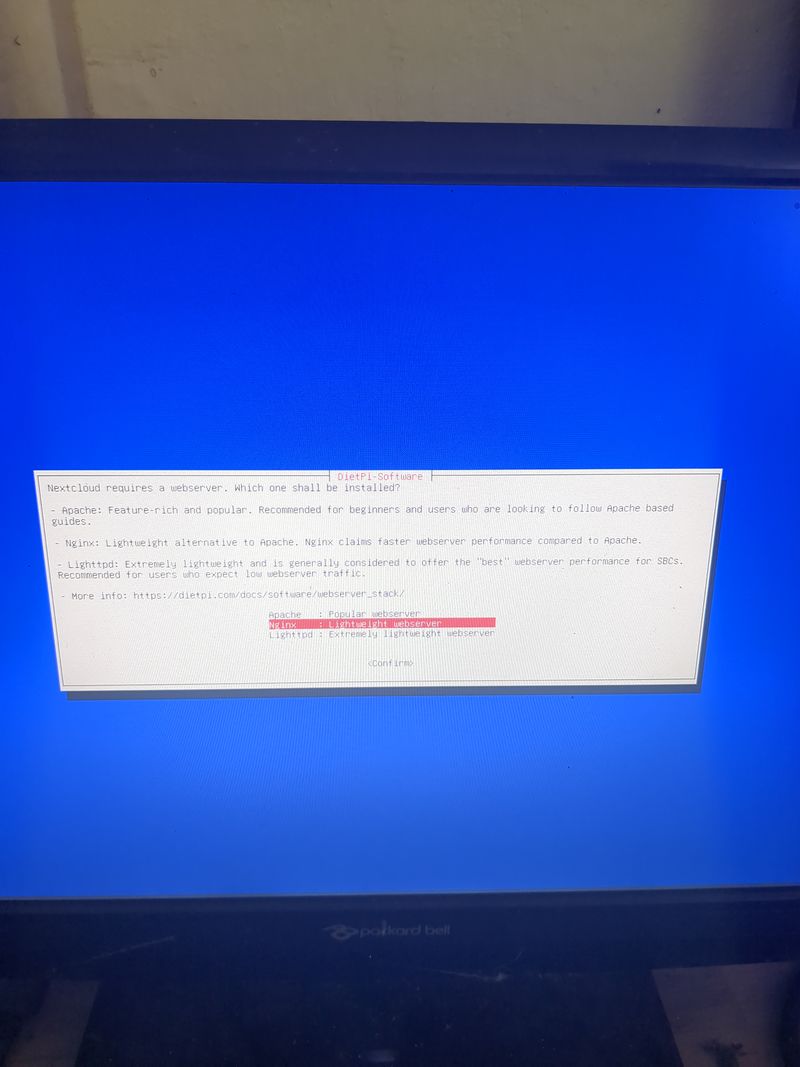
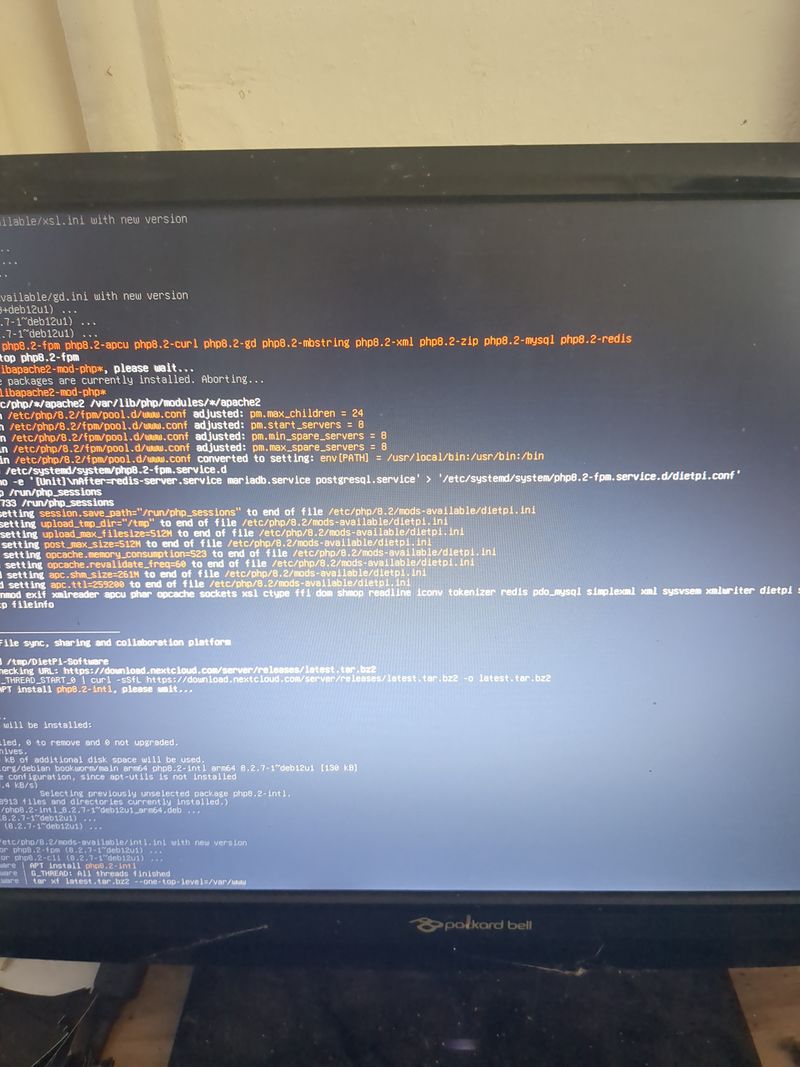
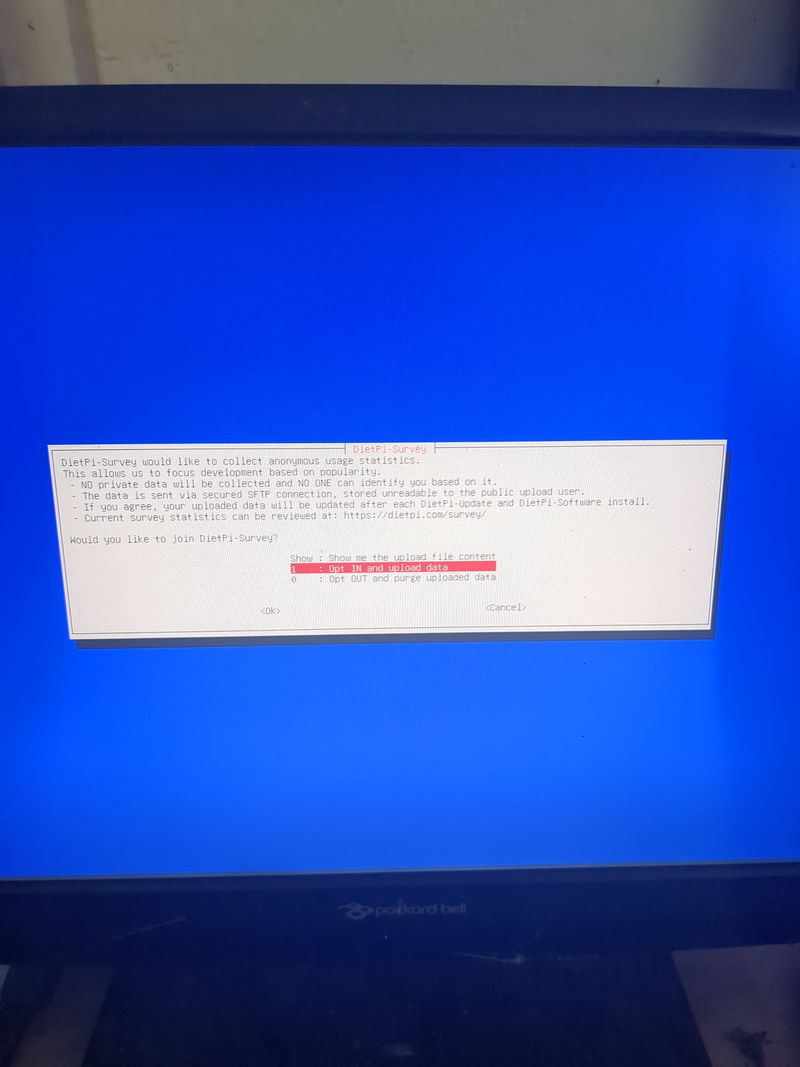
Follow the menus at first boot to install the nextcloud service. It is very easy, it is in english and everything is automated. I have put the images of the menus you have to select.
Vous pouvez vous déplacer dans les menus au clavier avec les fleches et la touche tab.
Selectionner avec espace et valider avec entree.
Voir images des étapes 3 à 6 pour le déroulement de l'installation et les entrées à sélectionner.
Étape 6 - configuration du reseau local ethernet ou wifi
Si vous n'avez pas de box et que vous avez un orangepi ou un raspberrypi et que vous voulez vous connecter à un wifi (par exemple le wifi d'un smartphone en partage de connexion)
Dietpi fournit un utilitaire pour configurer automatiquement le wifi qui fonctionne sur raspberry. Chez moi ca ne fonctionne que si le réseau est en wpa2. Si vous voulez activer le WPA3 ou si vous voulez configurer votre wifi à la main, voici les étapes à suivre.
Linux est un peu compliqué pour la gestion des réseaux. Il existe une multitude de programmes permettant de gérer les réseaux (networking, network interfaces, ifup, wpa_supplicant, network_manager, ifconfig, ip...).
Si vous vous y connaissez je vous laisse choisir ce qui vous convient le mieux.
Sinon, on utilisera les programmes installés par défaut dans dietpi pour la gestion des interfaces wifi : wpa_supplicant et dhclient.
Commencer par brancher un adaptateur usb wifi à votre orangepi ou verifier que votre adaptateur wifi sur votre raspberry pi est bien détecté.
Sur un orangepi: verifier que l'adaptateur est bien détecté en tapant
lsusb
Cette commande va lister les périphériques usb et vous devriez voir votre clé usb wifi dans la liste. Verifier ensuite que les drivers de votre clé ont bien été chargés en tapant:
dmesg
Étape 7 - configuration d'un vpn wireguard pour rendre accessible votre serveur depuis une box 4g ou un modem 4g
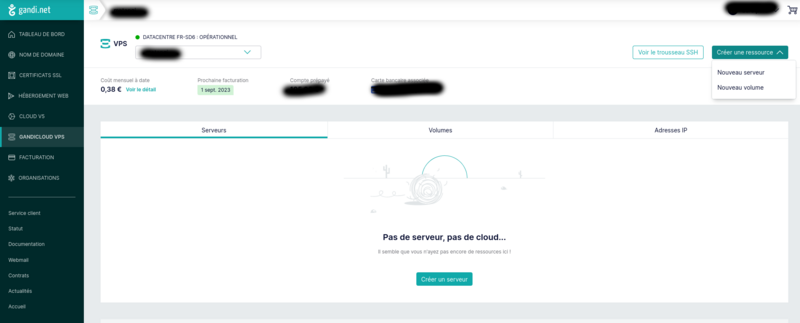
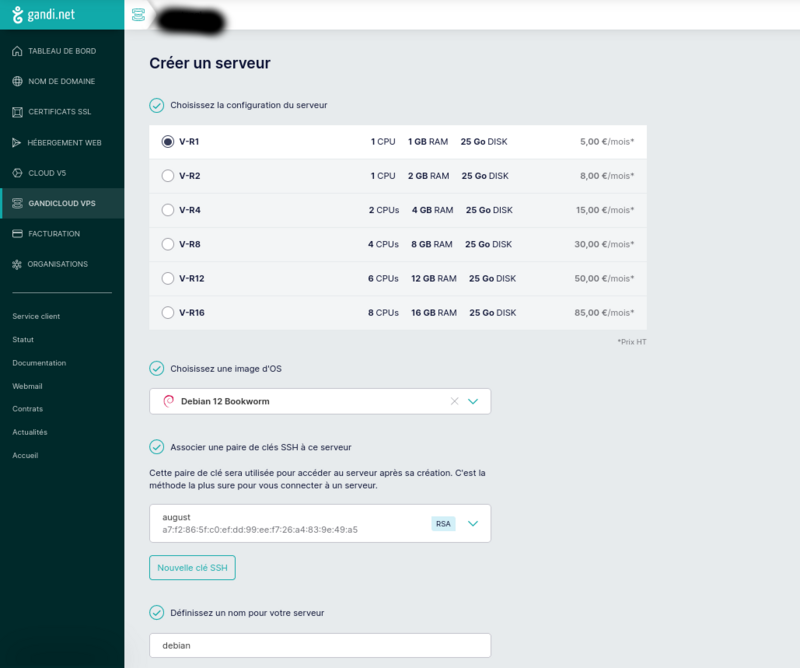
[ATTENTION, cette section remet en question le marché des vpns!!] Cette section n'est utile que pour les connections 4G ou en wifi sur téléphone (4G ou 5G) La 4g a l'avantage d'être mobile, avec une tres faible consommation du modem autour de 5W, et vous pouvez trouver des modems 4g sans wifi pour limiter la surface d'attaque de votre serveur (exemple netgear lm1200 autour de 150€). qu'est ce qu'un vpn? Les VPN sont principalement connus pour les "clients" vpn. C'est à dire que vous l'utilisez sur votre ordinateur pour vous "anonymiser". Le vpn est en fait un tunnel entre votre ordinateur et un ordinateur distant à partir duquel partent vos requetes vers internet. Tout votre traffic en direction d'internet va passer par ce tunnel. Internet pense ainsi que vos requetes proviennent de cet ordinateur distant. C'est à dire que votre ip publique devient celle de cet ordinateur distant. Votre fournisseur d'accès ne voit que le traffic entre votre ordinateur et cet ordinateur distant, ce qui vous "anonymise". En réalité, vous êtes anonyme vis à vis de votre fournisseur d'acces à internet, mais vous ne faites que déplacer la confiance vers votre fournisseur vpn qui lui peut voir votre traffic. Le vpn a aussi d'autres utilités comme vous donner accès à des sites qui filtrent l'accès selon la "provenance" de votre adresse ip publique. Vous pouvez tout à fait créer votre propre serveur vpn, et dans notre cas, ce serveur vpn permettra de rediriger les requetes internet faites sur ce serveur vers votre orange pi/raspberry pi en passant par le tunnel (dans l'autre sens que lorsque vous l'utilisez en tant que client pour accéder à internet). Et nous allons voir comment. Créer un serveur sur gandi.net Créer un compte sur gandi.net, puis créer un serveur dans gandicloud vps. Voir les images jointes pour la création en 3 clics du serveur qui coute 5€/mois. Pour créer une clé ssh et se logger voir https://docs.gandi.net/fr/hebergement_web/connexion/cle_ssh.html https://docs.gandi.net/fr/cloud/operations_courantes/connexion_serveur.html Une fois loggé sur le serveur, lancer la commande pour installer wireguard et les dépendances nécessairesLancer la même commande sur votre orange pi/raspberry pi. lancer ensuite les commandes suivantes sur votre serveur et sur le orange pi/raspberry pi pour creer les cles privés et publiques de wireguardsudo apt update && sudo apt install wireguard resolvconf iptables nano -y
Afficher la clé publique sur votre orange pi/raspberry pi en tapantsudo mkdir -p /etc/wireguard
sudo sh -c 'wg genkey | (umask 0077 && tee /etc/wireguard/private_key) | wg pubkey > /etc/wireguard/public_key'
Afficher egalement la clé publique sur votre serveur en tapantsudo cat /etc/wireguard/public_key
Entrer ensuite les commandes suivantes pour créer un fichier de configuration /etc/wireguard/wg0.conf sur votre serveur: Taper les lignes suivantes (remplacer cle_publique_du_orange_pi_ou_raspberry_pi par celle affichée précédemment) :sudo cat /etc/wireguard/public_key
Entrer ensuite la commande suivante sur le serveur pour lancer et activer le service vpnecho "[Interface]" | sudo tee /etc/wireguard/wg0.conf
echo "Address=10.10.0.1/24" | sudo tee -a /etc/wireguard/wg0.conf
echo "PrivateKey=$(sudo cat /etc/wireguard/private_key)" | sudo tee -a /etc/wireguard/wg0.conf
echo "ListenPort=12345" | sudo tee -a /etc/wireguard/wg0.conf
echo "[Peer]" | sudo tee -a /etc/wireguard/wg0.conf
echo "PublicKey=cle_publique_du_orange_pi_ou_raspberry_pi" | sudo tee -a /etc/wireguard/wg0.conf
echo "AllowedIPs=10.10.0.2/32" | sudo tee -a /etc/wireguard/wg0.conf
taper ensuitesudo systemctl start wg-quick@wg0
sudo systemctl enable wg-quick@wg0
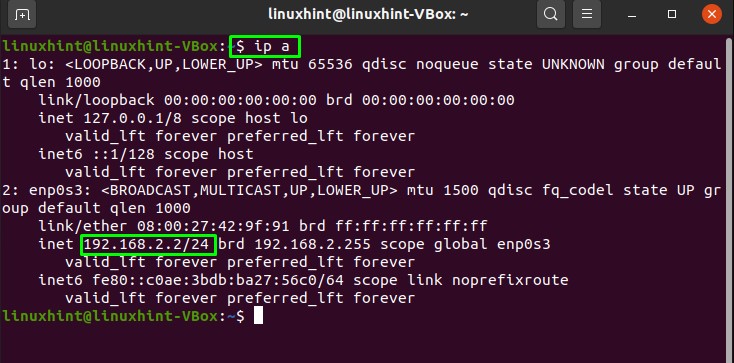
pour obtenir l'ip publique de votre serveur Taper les lignes suivantes (remplacer cle_publique_du_serveur par celle affichée précédemment et ip_publique_du_serveur par celle affichée précédemment) :curl ifconfig.me
La ligne AllowedIPS définit les ips de destination (sortantes) qui passeront par le tunnel et seront chiffrées mais aussi les ips entrantes autorisées. Si vous souhaitez configurer votre "client" (orange pi ou raspberry pi) pour utiliser le vpn pour accéder à internet, remplacer AllowedIPs=10.10.0.1/32 par AllowedIPs=0.0.0.0/0 En définissant 0.0.0.0/0 on indique que tout le traffic du orange pi/raspberry pi passera par le tunnel wireguard et toutes les ip entrantes seront autorisées. Il est alors important de bien configurer son firewall sur le serveur! Pour vérifier que wireguard fonctionne, lancer la commande suivante sur le serveur vpn:echo "[Interface]" | sudo tee /etc/wireguard/wg0.conf
echo "Address=10.10.0.2/24" | sudo tee -a /etc/wireguard/wg0.conf
echo "PrivateKey=$(sudo cat /etc/wireguard/private_key)" | sudo tee -a /etc/wireguard/wg0.conf
echo "[Peer]" | sudo tee -a /etc/wireguard/wg0.conf
echo "PublicKey=cle_publique_du_serveur" | sudo tee -a /etc/wireguard/wg0.conf
echo "AllowedIPs=10.10.0.1/32" | sudo tee -a /etc/wireguard/wg0.conf
echo "Endpoint=ip_publique_du_serveur:12345" | sudo tee -a /etc/wireguard/wg0.conf
Le ping doit fonctionner Ca ne fonctionne de façon systématique chez moi, mais je suis sur que si vous essayez loin de l'oeil de sauron votre météo numérique ira mieux que la mienne, et ca fonctionnera chez vous ;)ping 10.10.10.2 -c 4
Étape 8 - configuration d'un vpn openvpn pour rendre accessible votre serveur depuis une box 4g ou un modem 4g
Dans le cas où ca ne fonctionnerait pas avec wireguard, vous pouvez utiliser openvpn, (qui est configurable sans ligne de commande à la souris!). Configuration du serveur proxy gandi.net:Pour cela suivez les étapes suivantes (https://openvpn.net/vpn-server-resources/installing-openvpn-access-server-on-a-linux-system/): Update du 27/11/23: il n'y a pas de version bookworm d'openvpn-as disponible pour debian. Pensez à installer debian version bullseye
Si les commandes ci-dessus ne fonctionnent pas, il est possible qu'openvpn ait mis a jour des éléments. Merci alors de se reporter à https://openvpn.net/access-server/, s'inscrire, et suivre les instructions d'installation Rendez vous ensuite sur la page de configuration du serveur: https://<adresse_ip_du_serveur> login:openvpn password: indiqué dans le log de l'installationapt update && apt -y install ca-certificates wget net-tools gnupg
wget https://as-repository.openvpn.net/as-repo-public.asc -qO /etc/apt/trusted.gpg.d/as-repository.asc
echo "deb [arch=amd64 signed-by=/etc/apt/trusted.gpg.d/as-repository.asc] http://as-repository.openvpn.net/as/debian bullseye main" | sudo tee /etc/apt/sources.list.d/openvpn-as-repo.list
apt update && apt -y install openvpn-as
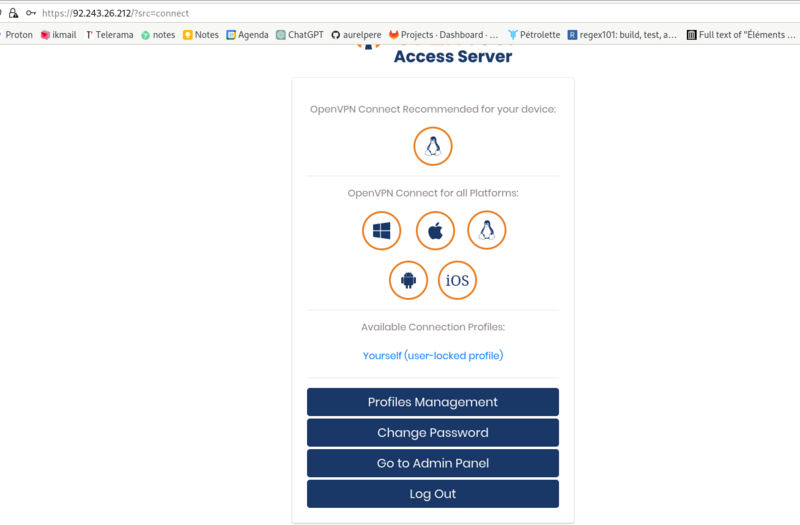
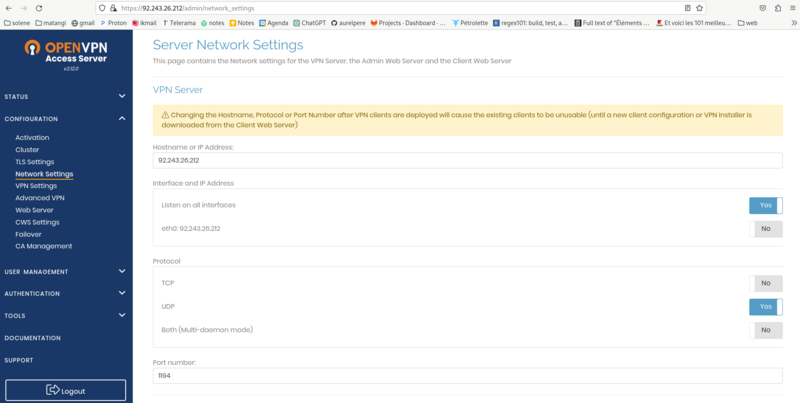
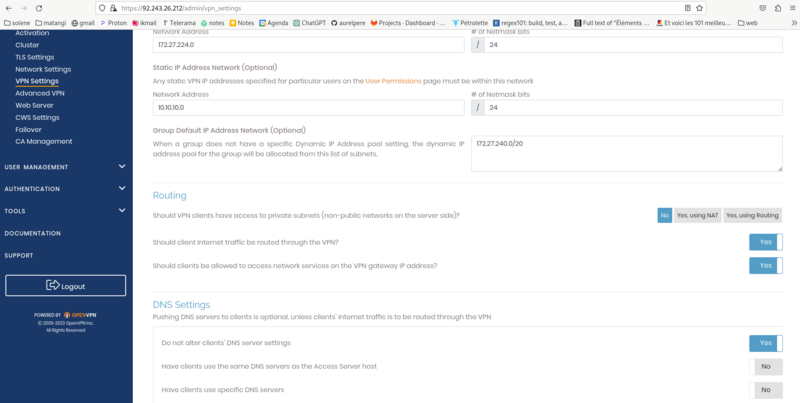
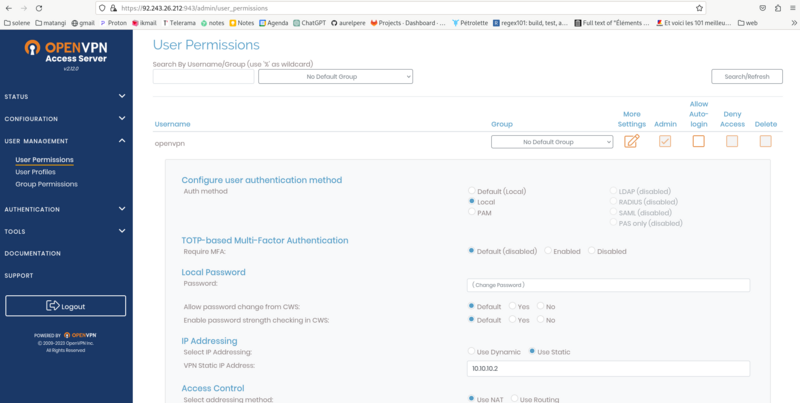
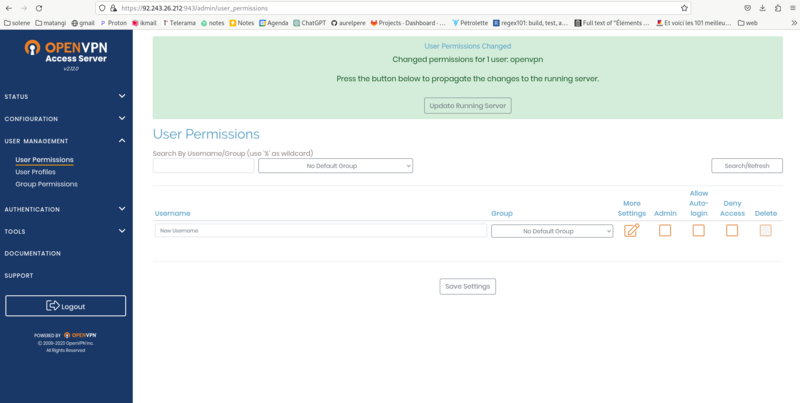
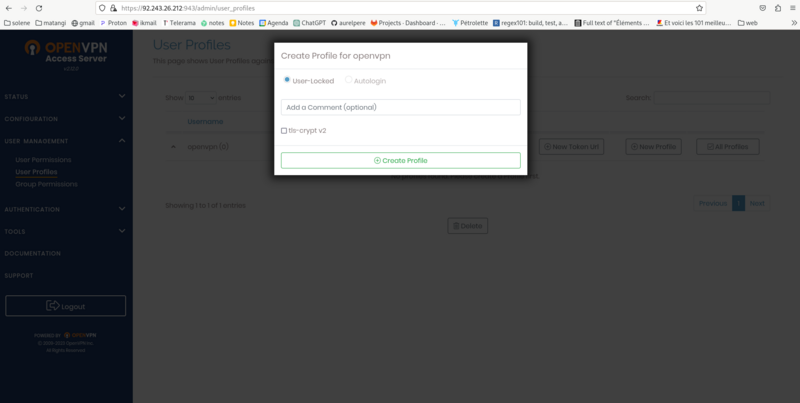
screen 1: go to admin panel reentrer vos login/password screen2: Network settings: Activer UDP seulement et port 1194 puis save settings screen3: VPN Settings: remplir les champs comme indiqué sur le screenshot puis save settings screen 4 et 5: User Management/User permission : changer le mot de passe dans local password et entrer l'adresse ip fixe du screeenshot puis save settings. Puis update running server.
Pour vous reconnecter à l'interface de configuration: https://adresse_ip_du_serveur:943 screen 6: User Management/User profile: cliquer sur new profile puis Cliquer sur create profile.
Renommer le fichier de configuration téléchargé en openvpn.conf Ouvrir le fichier de configuration et trouver la ligne auth-user-pass et la remplacer par la ligne suivante:
Configuration du orangepi/raspberrypiauth-user-pass auth.txt
Lancer ensuite sur le orangepi raspberry pi:
sudo apt update && sudo apt install openvpn
Copier le fichier de configuration télécharger vers /etc/openvpn/client/openvpn.conf sur votre orangepi/raspberry pi
creer un fichier auth.txt dans /etc/openvpn/client/ dans lequel vous copiez les deux lignes suivantes en remplacant password par votre mot de passe:
openvpn
password
Lancer ensuite le client vpn:
Si vous voulez que le client se connecte automatiquement au lancement de la machine tapersudo systemctl start openvpn-client@openvpn
sudo systemctl enable openvpn-client@openvpn
Étape 9 - Rediriger les requetes du serveur vpn vers le orange pi-raspberry pi
Pour rediriger les requetes sur le serveur vers le orange pi / raspberry pi, on met en place un serveur logiciel web nginx:On ouvre ensuite le fichier de configuration de ce logiciel serveur web:sudo apt install nginx -y
Remplacer le contenu du fichier par ce qui suit:sudo nano /etc/nginx/sites-enabled/default
Nginx va rediriger les requetes faites sur l'ip publique de votre serveur vers le nextcloud de votre orange pi / raspberry pi (ligne proxy_pass http://10.10.0.2;) Vous pouvez tester si cela fonctionne en vous rendant sur la page: http://ip_publique_de_votre_serveur_gandi/nextcloud/ (notez bien que c'est en http et pas https) Attention, de nombreux navigateurs n'acceptent plus tres bien les redirections en http, voir la section https pour configurer le https (il faudra prendre un nom de domaine).server { listen 80; server_name localhost; server_tokens off; add_header Permissions-Policy "accelerometer=(),autoplay=(),camera=(),display-capture=(),document-domain=(),encrypted-media=(),fullscreen=(),geolocation=(),gyroscope=(),magnetometer=(),microphone=(),midi=(),payment=(),picture-in-picture=(),publickey-credentials-get=(),screen-wake-lock=(),sync-xhr=(self),usb=(),web-share=(),xr-spatial-tracking=()"; add_header Strict-Transport-Security "max-age=31536000 ; includeSubDomains"; add_header X-Frame-Options "SAMEORIGIN"; add_header X-Content-Type-Options nosniff; add_header Content-Security-Policy "script-src 'self';"; add_header X-Permitted-Cross-Domain-Policies none; add_header Referrer-Policy no-referrer; add_header Clear-Site-Data "cache,cookies,storage"; location / { proxy_pass http://10.10.0.2; proxy_set_header Host $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-Proto $scheme; client_max_body_size 20M; limit_except GET HEAD POST {deny all;} } }
Étape 10 - Nom de domaine et adresse fixe
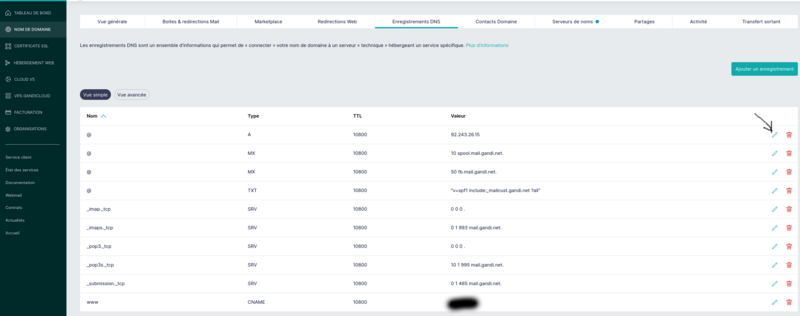
Le nom de domaine est l'adresse dans votre navigateur : par exemple lowtechlab.org. Il vous permet de rendre votre serveur accessible plus facilement avec une adresse facilement memorisable. Il ne fait qu'associer le nom de domaine à l'adresse ip de votre serveur vpn ou l'adresse ip de votre box. Que vous enregistriez un nom de domaine pour rediriger vers votre adresse ip ou pas (c'est nécessaire pour avoir le https cependant), il faut noter que par défaut, les fournisseurs d'accès vous octroient une adresse ip différente à chaque connexion. Si vous souhaitez une adresse ip fixe, il faut en faire la demande à votre fournisseur d'accès. Ce n'est malheureusement plus très répandue dans les offres grands publics. Orange propose à la place un "DynDns" qui vous propose une adresse en lettres correspondant à votre adresse ip mais à laquelle vous ne pouvez pas rattacher facilement un nom de domaine. Certains gestionnaires de nom de domaine, comme infomaniak, proposent tout de même d'enregistrer un nom de domaine pour le dyndns qui est acessible assez facilement sans surcout chez les principaux opérateurs. Si vous avez un accès en 4G, il n'est pas possible d'avoir une adresse ip fixe et votre adresse ip publique correspondra à un "pool". C'est à dire que l'opérateur alloue une adresse ip publique pour plusieurs clients, ne vous permettant pas d'utiliser la technique du NAT/Port Forwarding pour rendre votre dietpi accessible sur internet. Il faudra alors prendre un nom de domaine pour votre serveur vpn qui redirige les requetes vers votre dietpi. Voir image jointe pour l'enregistrement d'un nom de domaine: c'est la ligne nom "@" type A qu'il faut renseigner avec l'adresse ip publique de votre box ou de votre serveur vpn.
Étape 11 - Configuration https sur serveur gandi vpn
Si vous avez un serveur proxy Sur votre serveur gandi, effectuer les opérations suivantes: Creer un fichier /etc/nginx/conf.d/dietpi.conf et copier les lignes suivante:lancer ensuite les commandes suivantes:server { listen 80; server_name localhost; server_tokens off; add_header Permissions-Policy "accelerometer=(),autoplay=(),camera=(),display-capture=(),document-domain=(),encrypted-media=(),fullscreen=(),geolocation=(),gyroscope=(),magnetometer=(),microphone=(),midi=(),payment=(),picture-in-picture=(),publickey-credentials-get=(),screen-wake-lock=(),sync-xhr=(self),usb=(),web-share=(),xr-spatial-tracking=()"; add_header Strict-Transport-Security "max-age=31536000 ; includeSubDomains"; add_header X-Frame-Options "SAMEORIGIN"; add_header X-Content-Type-Options nosniff; add_header Content-Security-Policy "script-src 'self';"; add_header X-Permitted-Cross-Domain-Policies none; add_header Referrer-Policy no-referrer; #add_header Clear-Site-Data "cache,cookies,storage"; return 301 https://$host$request_uri; location / { return 301 https://$host$request_uri; } }
obtenir les certificats (rempalcer __domain__ par votre domaine):sudo apt install letsencrypt
wget https://raw.githubusercontent.com/certbot/certbot/master/certbot-nginx/certbot_nginx/_internal/tls_configs/options-ssl-nginx.conf
sudo cp options-ssl-nginx.conf /etc/letsencrypt/options-ssl-nginx.conf
wget https://raw.githubusercontent.com/certbot/certbot/master/certbot/certbot/ssl-dhparams.pem
sudo cp ssl-dhparams.pem /etc/letsencrypt/ssl-dhparams.pem
sudo rm /etc/nginx/sites-enabled/default
sudo apt remove certbot
sudo apt install python3-certbot-nginx
copier ensuite les lignes suivante dans votre fichier /etc/nginx/conf.d/dietpi.conf en remplacant __domain__ par votre domainesudo certbot certonly --nginx -d __domain__
redémarrer nginxserver { listen 80; server_name localhost; server_tokens off; add_header Permissions-Policy "accelerometer=(),autoplay=(),camera=(),display-capture=(),document-domain=(),encrypted-media=(),fullscreen=(),geolocation=(),gyroscope=(),magnetometer=(),microphone=(),midi=(),payment=(),picture-in-picture=(),publickey-credentials-get=(),screen-wake-lock=(),sync-xhr=(self),usb=(),web-share=(),xr-spatial-tracking=()"; add_header Strict-Transport-Security "max-age=31536000 ; includeSubDomains"; add_header X-Frame-Options "SAMEORIGIN"; add_header X-Content-Type-Options nosniff; add_header Content-Security-Policy "script-src 'self';"; add_header X-Permitted-Cross-Domain-Policies none; add_header Referrer-Policy no-referrer; #add_header Clear-Site-Data "cache,cookies,storage"; return 301 https://$host$request_uri; location / { return 301 https://$host$request_uri; } } server { listen 443 ssl http2; server_name localhost; server_tokens off; ssl_certificate /etc/letsencrypt/live/__domain__/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/__domain__/privkey.pem; include /etc/letsencrypt/options-ssl-nginx.conf; ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; add_header Permissions-Policy "accelerometer=(),autoplay=(),camera=(),display-capture=(),document-domain=(),encrypted-media=(),fullscreen=(),geolocation=(),gyroscope=(),magnetometer=(),microphone=(),midi=(),payment=(),picture-in-picture=(),publickey-credentials-get=(),screen-wake-lock=(),sync-xhr=(self),usb=(),web-share=(),xr-spatial-tracking=()"; add_header Strict-Transport-Security "max-age=31536000 ; includeSubDomains"; add_header X-Frame-Options "SAMEORIGIN"; add_header X-Content-Type-Options nosniff; add_header Content-Security-Policy "script-src 'self';"; add_header X-Permitted-Cross-Domain-Policies none; add_header Referrer-Policy no-referrer; #add_header Clear-Site-Data "cache,cookies,storage"; location / { proxy_pass http://10.10.10.2; proxy_set_header Host $host; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-Proto $scheme; client_max_body_size 20M; limit_except GET HEAD POST {deny all;} } }
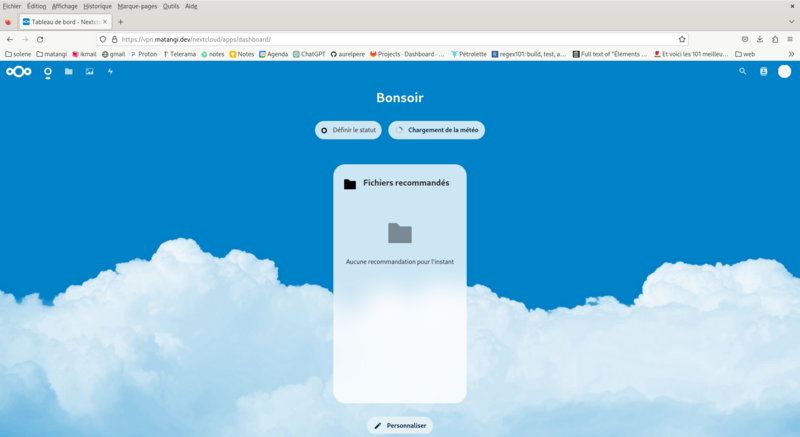
Une fois ces étapes réalisées, votre serveur est accessible en ligne en https en tapant dans votre navigateur https://votre_domaine/nextcloud/ Vous pouvez alors configurer nextcloud en ligne par le compte administrateur login par défaut sur dietpi: admin mot de passe par défaut sur dietpi: mot de passe entrée à l'installation de dietpisudo systemctl restart nginx
Étape 12 - Configuration https sur dietpi si vous etes branché en box
Je n'ai pas de box, je vous updaterai quand ce sera le cas et prooftesté! :)
Étape 13 - Rendre votre serveur nomade et autonome énergétiquement en photovoltaique
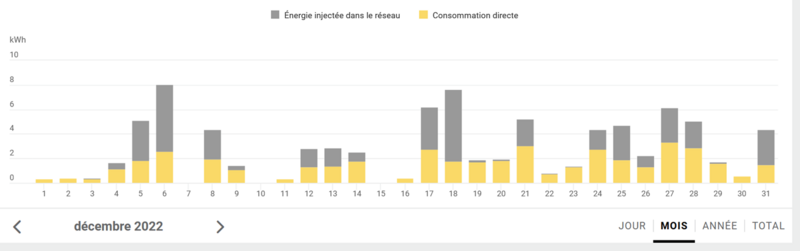
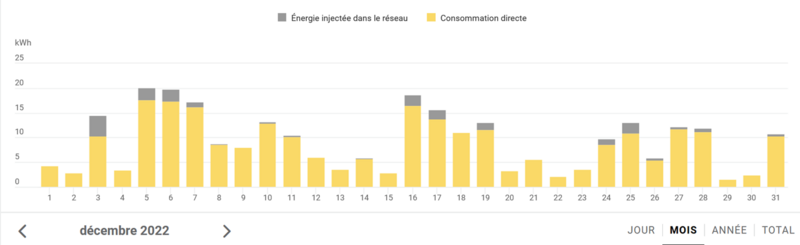
Que ce soit pour des raisons écologiques, ou pour d'autres raisons, il est intéressant d'avoir un serveur autonome énergétiquement, qui ne dépendra pas des aléas du réseau électrique. NB: pour une version légèrement modifié du dimensionnement photovoltaïque (production moyenne/par intervalle calée sur modèle jrc en décembre au lieu du nombre d'heure d'ensoleillement minimum), voir mon autre tuto ici: Dimensionner une installation photovoltaïque autonome videos: bases debutant(panneaux, regulateur, onduleur, conso/prod): https://www.youtube.com/watch?v=8Ft4XQj9lQ4 montage simple kit myshop solaires pour 230V: https://www.youtube.com/watch?v=SvmPEhPq_S8 kit prêts à acheter (si vous avez des subventions et des collègues qui coopèrent bien): https://allo.solar/kit-solaire-1650w-230v-autoconsommation-aps.html?gclid=EAIaIQobChMIkY_fxvu-gAMVyLfVCh014gadEAYYASABEgJd8_D_BwE solution de stockage intermédiaire intégrée (cher et pas tres lowtech): Station énergie portable extensible 230V BLUETTI AC200MAX EcoFlow River 2 pro kits semi lowtech (celui utilisé dans ce guide): panneaux photovoltaïque 120W et batterie de voiture plomb acide. kit vraiment lowtech: fabriquer sa batterie lithium à partir de déchets: voir barnabé chaillot https://www.youtube.com/watch?v=_hwj7Ds50lU rappel de base: branchement en série (+ sur - et + sur -) on ajoute le voltage et on garde le meme amperage, branchement en paralelle (+ sur +, - sur -) on ajoute l'amperage et on garde le meme voltage idem pour les batteries: à mettre en paralelle pour garder la meme tension (voltage) La première problématique du photovoltaïque lowtech autonome est le dimensionnement de l'installation (Se reporter à mon autre tuto Dimensionner une installation photovoltaïque autonome) Pour cela on trouve pas mal d'informations sur internet. Vous pouvez utiliser la feuille libreoffice en piece jointe en haut de ce tutoriel pour du dimensionnement "bricolé". Le dimensionnement - le besoin journalier: Le orange pi consomme environ 20W Un disque usb supplémentaire consomme environ 5W Un modem 4G consomme environ 5W Soit un besoin constant de 35W en prenant 16% de marge d'erreur. Le besoin journalier pour un serveur qui tourne 24h/24: 35W*24h=840Wh Le besoin journalier pour un serveur qui tourne en journéee seulement: en été: 35W*14h=490Wh en hiver: 35W*8h=280Wh Notez qu'il s'agit là d'un besoin moyen et si vous souhaitez dimensionner pour des usages divers, il est recommander de procéder de façon plus précise en calculant les besoins temps réels. Le dimensionnement du stockage par le temps d'autonomie : Estimer les pertes à 20% et augmenter le besoin en consquénce: besoin 24h/24=840/0,80=1050Wh Estimer le temps d'autonomie voulue: exemple 24h On va alors dimensionner le stockage pour tenir 24h. Pour des batteries en 12V: 1050Wh/12V=87,5Ah Etant donné qu'on veut limiter la décharge des batteries à 50%, on prendra donc 87,5Ah/0,5=175Ah Soit 2100 Wh en 12V Selon les caractéristiques des panneaux (voir feuille de calcul), on peut estimer la recharge de la batterie lorsque l'ensoleillement est minimal (en décembre). Le dimensionnement par la méthode du nombre de jours voulues pour recharger entierement les batteries: Si on veut pouvoir recharger les batteries en un jour en hiver, il faut considérer la puissance produite par vos panneaux au jour d'hiver avec le moins d'ensoleillement. Si on prend 3,5h pour le minimum, le nombre de panneaux nécessaire de puissance x Watt sera: C_batterie:Capacité batterie en Wh Dans notre exemple 2100Wh T_hiver:temps de recharge journalier minimal en hiver (en h) Dans notre exemple 3,5h B_hiver:besoin journalier hors temps ensoleillement en hiver (en Wh) Dans notre exemple (24h-3,5h)*35W=897Wh n_voulus:nombre de jour voulus pour recharger entierement la batterie Dans notre exemple 1 I:amperage sortie d'un panneau photovoltaique Dans notre exemple 7A U:tension sortie d'un panneau photovoltaique Dans notre exemple 12V Nb_panneaux=C_batterie+B_hiver*n_nvoulus/T_hiver*I*U*n_voulus Dans l'exemple: Nb_panneaux=(2100+897*1)/(3,5*12*7*1) Il faudra donc 10 panneaux de 84W de 7A 12V Noter que la valeur cardinale ici est à la ligne 42 du fichier joint, il s'agit de l'ensoleillement journalier minimal en décembre à production nominale. Des valeurs de référence peuvent être trouvées sur https://re.jrc.ec.europa.eu/api/v5_2/seriescalc?lat=44.203142&lon=0.616363&loss=14&angle=45&aspect=0&startyear=2005&endyear=2005&pvcalculation=1&peakpower=1&pvtechchoice=crystSi&browser=0&outputformat=csv Mais rien ne vaut une mesure empirique pour vérifier tout ca. Le graphique en illustration provient du monitoring de deux installations à 400km de distance d'une entreprise qui installe et suit du photovoltaïque depuis 2018. J'attend de mesurer tout ça avec un voltmetre fiable sur plusieurs panneaux achetés d'occasions pour updater ce tuto en décembre! :) Tout commentaire et "retour d'experience" est bienvenu à ce sujet en bas de cette page! Le dimensionnement par la méthode essais et erreurs La feuille de calcul propose aux lignes 41 et 42 d'ajuster le nombre de panneaux et le temps d'ensoleillement moyen en décembre et donne le besoin journalier hors temps ensoleillement hiver en Wh et la recharge batterie journaliere maximale en hiver (en Ah et Wh). En faisant des essais sur les deux paramètres, on peut obtenir le nombre de panneaux minimum pour que la(les) batterie(s) se recharge(nt) positivement en hiver. La problématique principale du photovoltaïque lowtech autonome est le stockage de l'énergie. Vous pouvez lire les caractéristiques des panneaux qu'on vous a donné ou trouvés sur leboncoin à pas cher: -puissance crete: elles s'aditionnent pour obtenir la puissance nécessaire trouvée lors de la phase de dimensionnement. -tension : 12V,24V ou 48V. voir regles série/paralelle pour leur additions -intensité: variable selon les modèles mais souvent inferieure à 10A. voir regles série/paralelle pour leur additions Pour recharger des batteries, en principe, si vous connectez votre panneaux en direct sur une batterie, il suffit que la tension à la sortie de vos panneaux soit la même que celles de vos batterie, et ca devrait charger. Il y a un composants importants à retenir pour charger correctement vos batteries: le regulateur ou controleur de charge il en existe de trois sortes: les tor (tout ou rien) les mppt (Maximum power point tracking) et les pwm (Pulse Width Modulation) Ils sont composés d'un adaptateur DC/DC (courant continu vers courant continu) et d'un coupe circuit. Le mppt comprend également un adaptateur d'impédence (il a une résistance pour adapter l'amperage injecté dans la batterie). Les mppt accepte des puissances nominales plus élevées, cad des tensions et intensité plus élevées. Le régulateur ou controleur de charge permet principalement de couper le circuit quand la batterie est rechargée en surveillant la tension et l'intensité de charge. Il coupe le circuit si leurs valeurs dépassent les intervalles de référence (pour cela le regulateur arrete la charge temporairement et mesure la tension aux bornes des batteries). Le mppt a un "algorithme" électronique intégré qui va chercher le point de puissance optimal grace a son adaptateur d'impedance. Si vous connectez plusieurs panneaux et plusieurs batteries, il est recommandé d'avoir un regulateur pour couper la charge correctement lorsque la batterie est chargée. Les tensions de charge de référence sont 12V,24V et 48V. Cependant, les prix des modèles augmentent avec la puissance nominales (qui va dépendre de l'amperage) qu'ils acceptent. Pour limiter l'intensité du courant de la production photovoltaïque, il est plus judicieux d'utiliser des panneaux de plus forte puissance qui sont généralement à des tensions plus élevées (rappel P=U*I, rappel E=P*t se conserve dans un systeme fermé). note: si le systeme de stockage par batterie ou l'appareil connecté à vos panneaux n'absorbe pas toute la puissance produite, et si le régulateur de charge ne coupe pas le circuit, le reste sera dégagé en chaleur. L'amperage va aussi dependre de la capacité de stockage de vos batteries, dimensionnées pour couvrir vos besoins pendant une periode définie au dimensionnement. Le courant de charge est calculé en divisant par 4 ou 5 la capacité nominale de la batterie exprimée en Ah qui devrait alors se recharger en 4 ou 5h. Cependant une batterie se rechargera aussi avec un courant de charge de la capacité nominale de la batterie divisée par 20 mais plus lentement (en 20h). Dimensionnez et/ou agencez vos panneaux en conséquence. Des montages de panneaux serie+paralelle peuvent permettrent d'ajuster tension et amperage. Il y a enfin un dernier point sur lequel être attentif: le déclenchement de la recharge de la batterie par le regulateur/controleur de charge (qui déclenche quand la tension de la batterie diminue en dessous d'un certain seuil). En effet, si la puissance soutirée à la batterie est trop faible, il est possible que le temps nécessaire à la décharger avec votre consommation journalière pour déclencher la recharge dans le régulateur dépasse le temps d'ensoleillement journalier. La batterie ne se recharge alors pas du tout pendant la journée. Dans ce cas, votre batterie ne se rechargera qu'un jour sur deux ou sur trois (selon le seuil de déclenchement de la recharge du regulateur). C'est un paramètre à prendre en compte dans le dimensionnement (non inclus dans la feuille de calcul). Le régulateur a 3 phases: 1.bulk: le regulateur laisse passer le courant 2.floating: le regulateur alterne interupteur fermée et ouvert à une fréquence donnée pour maintenir la batterie chargée En outre il faut prendre des précautions car la charge des batteries présente certains risques. 3.absorption (pour les mppt): la tension de charge augmente un peu pour créer une difference de potentiel suffisante pour continuer à charger la batterie presque pleine. En théorie le courant de charge diminue lorsque la batterie est presque rechargée (courant de queue etc.) La charge de batteries en paralelle ou en série sur des batteries usagées qui n'ont pas les mêmes tensions ou intensité présente en théorie des risques. En effet vous lirez un peu partout que la résistance des fils pour relier ces batteries créee des différences de potentiels entre les batteries qui produisent des décharges d'une batterie envers une autre etc. créant des risques d'explosion, de degazage pour les batteries plomb etc. Il faut bien se rapeller que les batteries sont des assemblages de composants unitaires de faible tension mis en séries et en paralelle pour obtenir un générateur de l'intensité et la tension voulue et qu'à priori faire de même avec des batterie entiere ne présente pas vraiment de risques.. On parle souvent de "battery management system" (bms) "intégré" pour les batteries lithium ion. En réalité le régulateur de charge est déjà un "bms". En théorie, le bms intégré s'assure que les tensions et les intensités de chaque unité composant la batterie est la même et la rééquilibre au besoin. On peut bien sûr s'interroger si tout ceci n'est pas une façon de rendre le stockage de l'énergie plus cher avec des composants BMS artificiellement chers et si ce n'est pas une façon d'éviter de réutiliser des unités de batteries usagées. Il est par exemple étonnant qu'il n'existe pas de BMS pour rééquilibrer automatiquement des batteries plomb acide, ce qui rendrait utilisable toutes les batteries mises au rebut de l'industrie automobile pour stocker l'énergie photovoltaïque sans risque! Dans tous les cas, si vous réutilisez des batteries au plomb, utilisez un régulateur pour éviter de continuer à charger vos batteries rechargées (risques de production d'hydrogene) -ou si vous n'en utilisez pas dimensionnez avec beaucoup de soin-, évitez les décharges profondes, et maintenez les batteries à une temperature constante autant que possible.
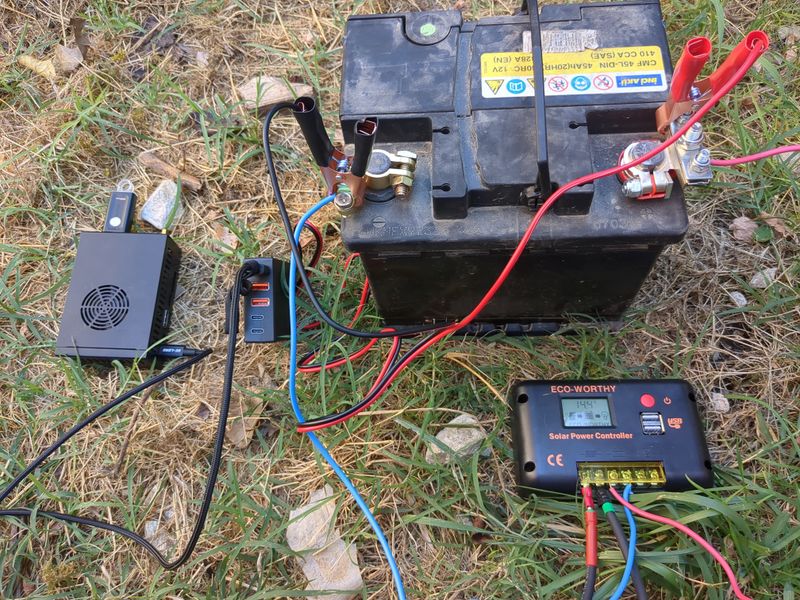
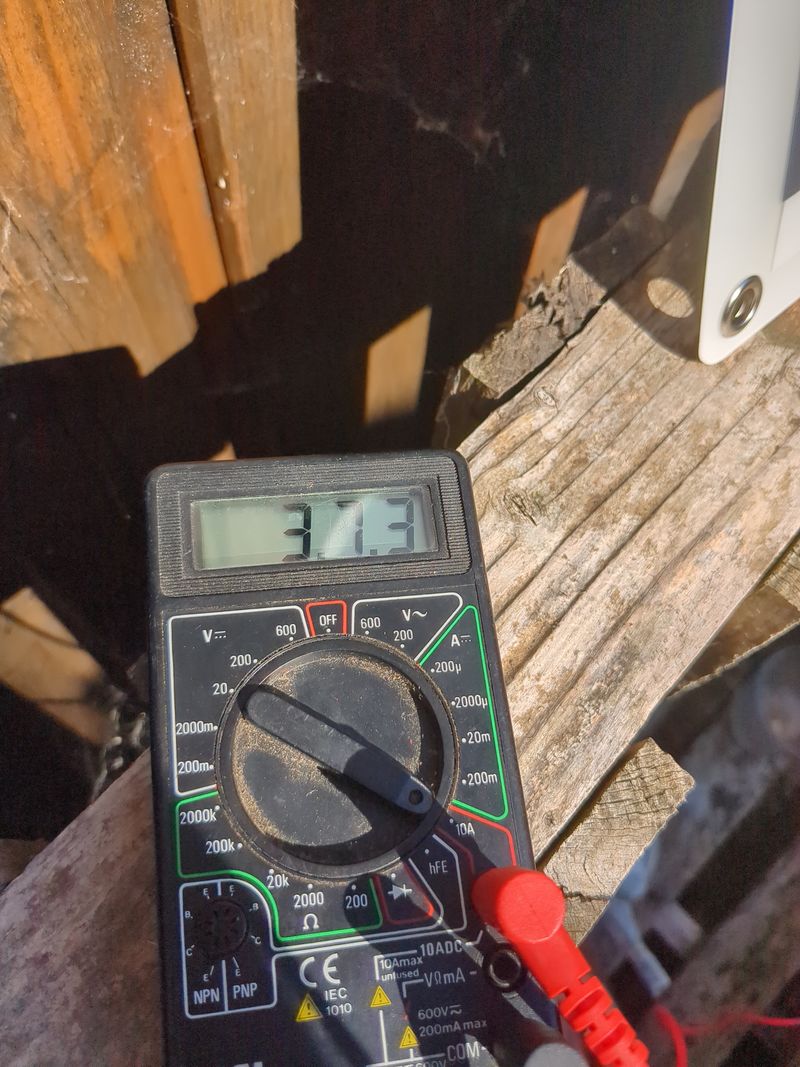
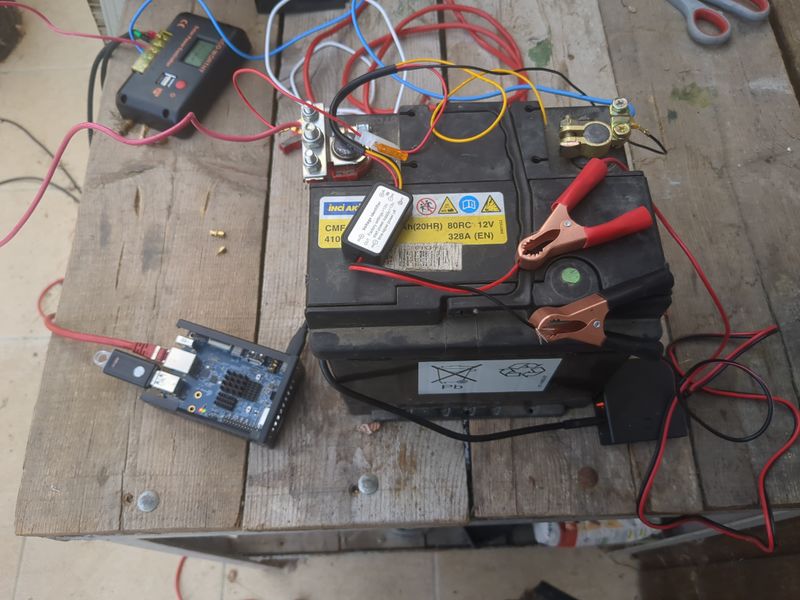
Étape 14 - Montage et test
On dimensionne sur un dixieme de la puissance de panneaux et un quart de la capacité de batterie de ce que la théorie nous a indiqué pour être autonome 24h/24h et en capacité de recharger en un seul jour en hiver, soit un panneau de 120W et une vieille batterie de voiture de 45Ah en 12V. C'est raccord avec une approche lowtech de ne faire tourner le serveur que lorsqu'il fait jour, pour une informatique qui respecte la temporalité humaine. Pour être bien en hiver (à hypothèse 3,5h d'ensoleillement moyen), il faudrait une batterie de plus de 58Ah, mais pour raisons budgétaire, on fait pour l'instant avec ce qu'on a! :). Le regulateur utilisé n'accepte pas les panneaux 40V donc on n'a pas utilisé le panneau photovoltaïque d'occasion de 180W à 20€ trouvé sur leboncoin, mais je ne manquerai pas d'updater ce tuto avec des raccordement de panneaux et de batteries dès que j'aurai le materiel et avec les valeurs de production hivernale si j'y arrive! Etapes de montage:#Raccorder un cable electrique de la borne + de la batterie à la borne + du regulateur pwm (sortie batterie). Raccorder un cable electrique de la borne - de la batterie à la borne - du regulateur pwm (sortie batterie) #Raccorder les panneaux aux cables mc4. Brancher le côté dénudé du cable + au + du régulateur pwm (entree panneaux). Brancher le côté dénudé du cable - au - du régulateur pwm (entree panneaux). #Brancher les pinces du convertisseur 12V batterie/5V USB avec le + sur le + et le - sur le - #Brancher le cable rj45 de votre box ou modem 4g au orange pi ou raspberry pi #Brancher le cable usb du orange pi ou raspberry pi au convertisseur 12V batterie/5V USB #Pour automatiser le fonctionnement quand il fait jour et éteindre quand il fait nuit, on utiliser un module DRL (Daytime Running Light) de voiture. Le module est un interupteur qui laisse passer le courant quand la tension est supérieure à 13V (quand le panneau solaire charge la batterie). L'interrupteur est à brancher borne + du IN sur le + de la batterie, borne - du IN sur le - de la batterie, borne + du out sur la pince rouge et borne - du out sur la pince rouge (entre la batterie et le convertisseur 12V batterie/5V USB). Attendre quelques minutes que ca boot. Et voilà , votre serveur nextcloud est accessible en ligne ! :) Notez que si vous voulez alimenter quelque chose en courant alternatif 220V, la seule chose qu'il manque au montage est un convertisseur DC/AC (courant continu alternatif) qu'on trouve facilement en magasin de camping car ou sur leboncoin.
Étape 15 - Securisation du serveur
Au niveau sécurité, les failles connues des cpus peuvent être trouvées sous linux en faisant:Cette commande sur le orange pi (cpu CortexA55) avec dietpi installé donne:grep -r . /sys/devices/system/cpu/vulnerabilities
Ayant testé un orange pi un raspberry pi et un odroid, le probleme reste le même./sys/devices/system/cpu/vulnerabilities/spectre_v2:Mitigation: Unprivileged eBPF enabled /sys/devices/system/cpu/vulnerabilities/itlb_multihit:Not affected /sys/devices/system/cpu/vulnerabilities/mmio_stale_data:Not affected /sys/devices/system/cpu/vulnerabilities/mds:Not affected /sys/devices/system/cpu/vulnerabilities/l1tf:Not affected /sys/devices/system/cpu/vulnerabilities/spec_store_bypass:Mitigation: Speculative Store Bypass disabled via prctl /sys/devices/system/cpu/vulnerabilities/tsx_async_abort:Not affected /sys/devices/system/cpu/vulnerabilities/spectre_v1:Mitigation: __user pointer sanitization /sys/devices/system/cpu/vulnerabilities/retbleed:Not affected /sys/devices/system/cpu/vulnerabilities/srbds:Not affected /sys/devices/system/cpu/vulnerabilities/meltdown:Not affected
basiques: on peut passer sa vie à augmenter la sécurité d'un systeme informatique... trouver le bon compromis et évaluer les risques ou appats en termes financiers. Le hack est toujours possible, et vu le nombre de failles 0day non encore publié, quel que soit le systeme d'exploitation, la question est moins d'avoir un système infaillible, que de savoir de qui on cherche à se protéger quand on cherche à "sécuriser" ou réduire sa surface d'attaque. Je pense que la philosophie libre reste supérieure en termes de sécurité car auditable et réparable plus vite par la "commu", mais il faut bien avouer que les reglages par défaut ne sont pas tip top car linux a été pensé pour être stable au départ (rappelez vous des écrans bleux windows il y a 30 ans), et pas "sécurisé". Ayant subi des hacks que je considère très avancés et pas à la portée du premier venu(et ce quel que soit le système d'exploitation, quelle que soit la machine, et quel que soit le niveau de sécurisation -hors compilation de kernel-), j'ai cherché à sécuriser mes dispositifs numériques et j'en arrive aujourd'hui à penser que la "souveraineté" numérique n'existe pas ou plus, les failles créent un marché de la sécurité, ca fait travailler des gens... Voir l'article intéressant de w0nderfall au sujet de la sécurité sous linux: https://wonderfall.space/linux-securite/ Cependant quelques éléments car c'est un sujet sur lequel on trouve peu d'informations didactiques rassemblées.
-principe de limiter surface d'attaque : principe général, la sécurisation ne fait que diminuer la surface d'attaque potentielle
-acces physique sécurisé et config logicielle liée:
- acces physique: à vous de voir -mot de passe grub
Lancer dans un terminal:
Copier le texte qui commence par grub.pbkdf2.sha512.10000.xy où xy est une longue suite de lettres et de chiffres Ajouter les lignes suivantes à un fichier /etc/grub.d/42_pw en remplacant user par votre nom d'utilisateur linux et pw par le texte précemment copiégrub-mkpasswd-pbkdf2
lancer ensuite la commandecat << EOF set superusers=user password_pbkdf2 pw EOF
-bons mots de passes en general pour changer le mot de passer de l'utilisateur courant taperupdate-grub
pour changer le mot de passe de l'utilisateur root taperpasswd
-éventuellement vérification d'intégrité du boot (voir ordinateurs de purism par exemple) -chiffrer (crypter) ses supports de stockage: https://doc.ubuntu-fr.org/tutoriel/chiffrer_ses_donnees https://www.dwarmstrong.org/remote-unlock-dropbear/ sécurité d'un serveur: -apt update automatisé : https://www.linuxtricks.fr/wiki/debian-activer-les-mises-a-jour-automatique-avec-unattended-upgrades -ssh renforcé : lignes à inclure dans votre configuration ssh (/etc/ssh/sshd_config):sudo passwd root
-firewall logiciel: ufw: https://doc.ubuntu-fr.org/ufw ou fichier de configuration iptables: https://gitlab.com/aurelpere/bp028-hardening/-/blob/main/rhel_iptables_ipv4/files/server_firewall.sh -backup: regle du 321 : 3 copies, 2 supports de stockages differents, 1 copie sur un autre lieux que les autres. borgbackup reste un standard pour sa fiabilité dans la communauté du libre (je confirme apres avoir testé plusieurs trucs) et offre un cloud pas cher pour stocker des sauvegardes "remote" qui finance le developpement de son logiciel libre. fail2ban: https://doc.ubuntu-fr.org/fail2ban fail2ban pour nextcloud: https://tuxicoman.jesuislibre.net/2015/01/fail2ban-pour-owncloud-7-sur-debian-jessie.html -desactiver ipv6 (ou configurer le firewall aussi pour ipv6) 3 méthodes pour désactiver ipv6: 1.dans grub 2.avec sysctl ajouter les lignes suivantes à /etc/systcl.confPort 22 #changer sur un autre port si vous le souhaitez Protocol 2 PermitRootLogin no StrictModes yes PermitEmptyPasswords no X11Forwarding no Ciphers chacha20-poly1305@openssh.com,aes256-gcm@openssh.com,aes128-gcm@openssh.com,aes256-ctr,aes192-ctr,aes128-ctr MACs hmac-sha2-512-etm@openssh.com,hmac-sha2-256-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-512,hmac-sha2-256,umac-128@openssh.com KexAlgorithms curve25519-sha256,curve25519-sha256@libssh.org,diffie-hellman-group14-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,ecdh-sha2-nistp521,ecdh-sha2-nistp384,ecdh-sha2-nistp256,diffie-hellman-group-exchange-sha256 AllowTcpForwarding no MaxSessions 1 UsePAM yes AllowUsers user #remplacer par les utilisateurs autorisées AllowGroups group #remplacer par les groupes autorisés PasswordAuthentication no AuthorizedKeysFile .ssh/authorized_keys
3.avec le network manager nmcli https://access.redhat.com/documentation/en-us/red_hat_enterprise_linux/8/html/configuring_and_managing_networking/using-networkmanager-to-disable-ipv6-for-a-specific-connection_configuring-and-managing-networking -sécuriser le serveur en cas de multi utilisateur ou autres utilisateurs ayant obtenu un accès: listes de fichiers à sécuriser (permissions etc.): https://linuxfr.org/forums/linux-general/posts/liste-des-fichiers-linux-a-securiser-owner-group-permissions-setuid-setgid-sticky-bit guides de durcissement anssi : https://www.ssi.gouv.fr/guide/recommandations-de-securite-relatives-a-un-systeme-gnulinux/ Pour aller plus loin en termes de sécurité: firewall physique libre: pcengines/ logiciel libre OPNSense fail2ban avec listes géographiques: https://thecustomizewindows.com/2016/11/fail2ban-geoip-action-script-block-ssh-country/ Créer un sas de connection à votre service en ligne (MySafeip): https://linuxfr.org/news/mysafeip-un-tiers-de-confiance-pour-votre-pare-feu sécuriser les services systemd linux: https://github.com/juju4/ansible-harden-systemd compiler un kernel : https://doc.ubuntu-fr.org/tutoriel/comment_compiler_un_kernel_de_kernel.org https://github.com/robertdebock/ansible-role-kernelnet.ipv6.conf.all.disable_ipv6 = 1 net.ipv6.conf.default.disable_ipv6 = 1 net.ipv6.conf.all.router_solicitations = 0 net.ipv6.conf.default.router_solicitations = 0 net.ipv6.conf.all.accept_ra_rtr_pref = 0 net.ipv6.conf.default.accept_ra_rtr_pref = 0 net.ipv6.conf.all.accept_ra_pinfo = 0 net.ipv6.conf.default.accept_ra_pinfo = 0 net.ipv6.conf.all.accept_ra_defrtr = 0 net.ipv6.conf.default.accept_ra_defrtr = 0 net.ipv6.conf.all.autoconf = 0 net.ipv6.conf.default.autoconf = 0 net.ipv6.conf.all.accept_redirects = 0 net.ipv6.conf.default.accept_redirects = 0 net.ipv6.conf.all.accept_source_route = 0 net.ipv6.conf.default.accept_source_route = 0 net.ipv6.conf.all.max_addresses = 1 net.ipv6.conf.default.max_addresses = 1
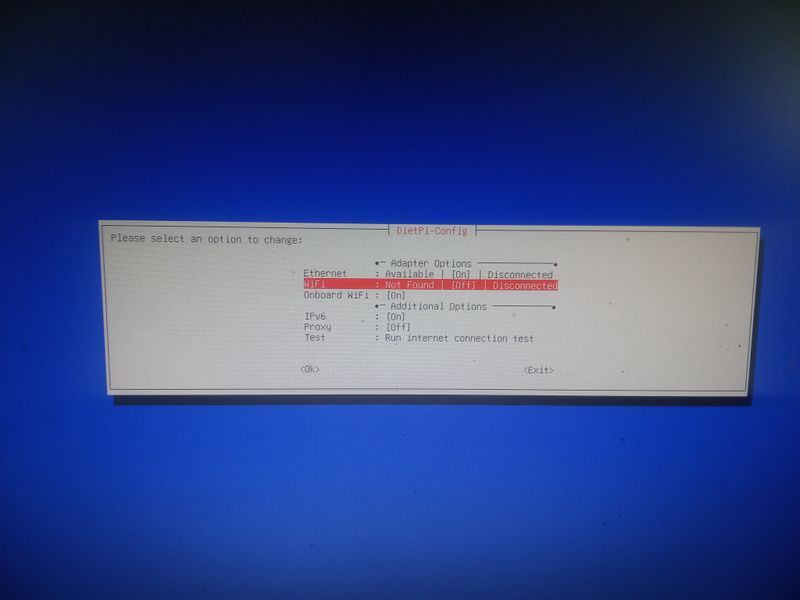
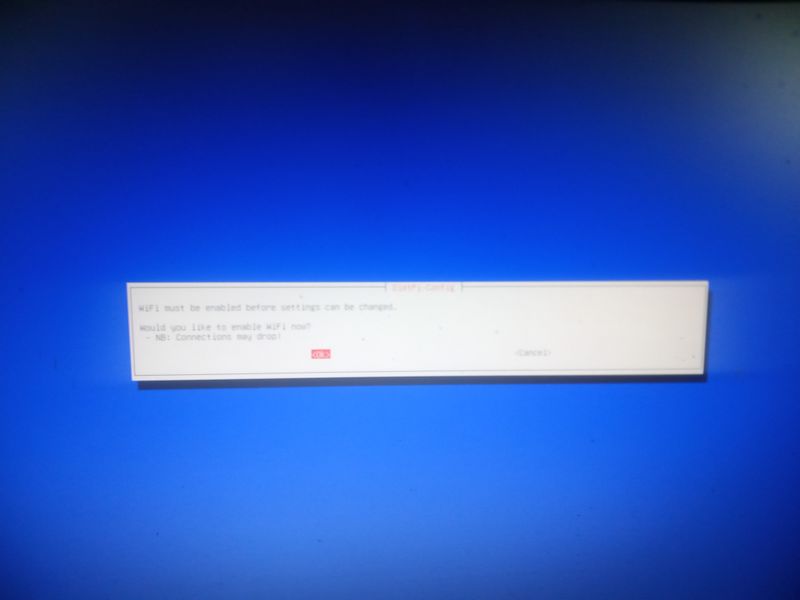
Étape 16 - Activer le wifi lors de l'installation (par exemple avec un raspberry)
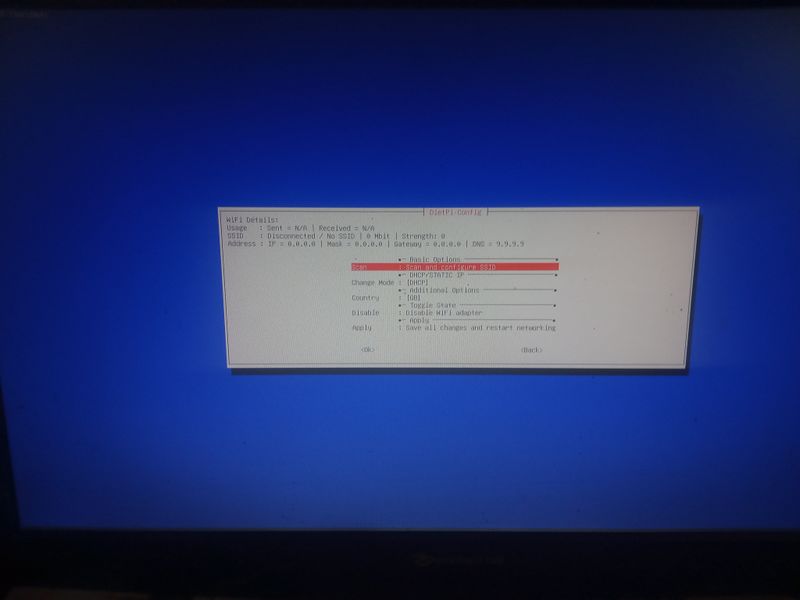
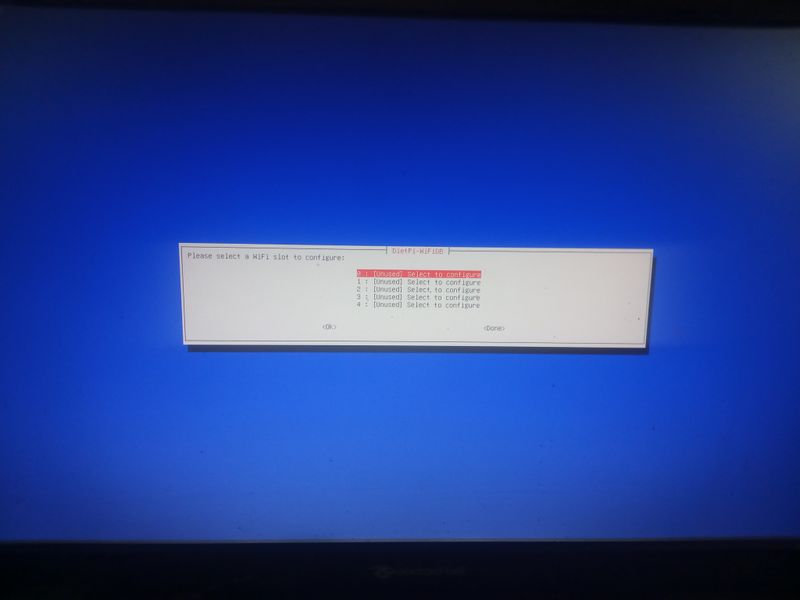
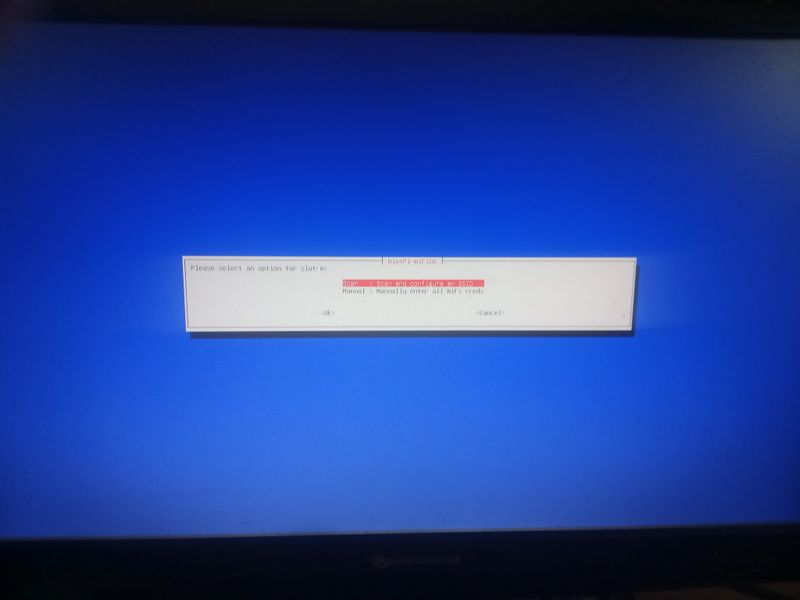
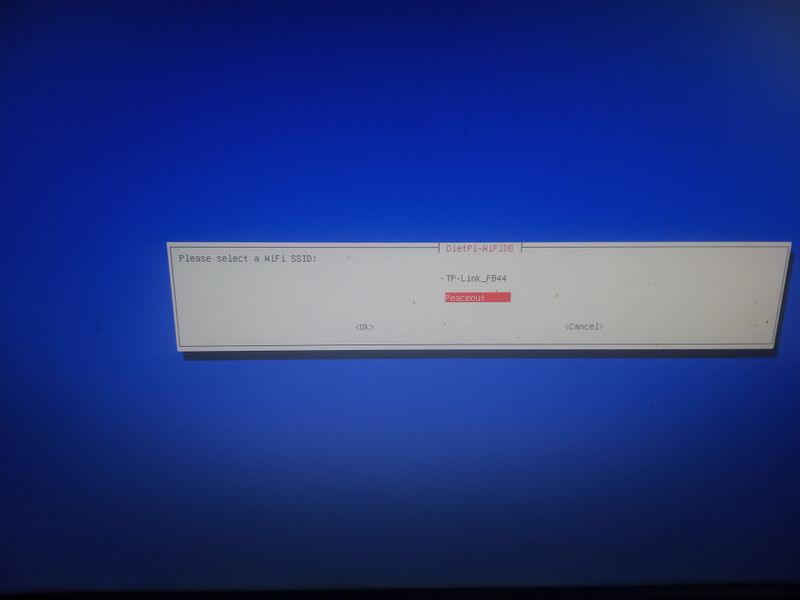
wpa2: Lorsque vous démarrez pour la premiere fois votre raspberry avec dietpi sur la clé usb ou la carte sd, le programme d'installation va vous afficher un menu suite à une erreur ("Checking ipv4 network connectivity") [...] ping: connect: Network is unreachabel") Aller alors dans "network-settings" puis suivez les menus indiqués dans les images jointes wpa3: voir etape 6
Notes et références
Pas de remerciements, c'est galère et on m'a pas aidé ;) Le tuto et son contenu ne sont pas issus d'expertise ou de formation spécifique mais de bidouillages et d'informations glanées ça et là donc soyez indulgents ;) Tout retour d'experience est bienvenu dans les commentaires
Published






 Français
Français English
English Deutsch
Deutsch Español
Español Italiano
Italiano Português
Português